Top 10 Web Application Pentesting Services for SaaS Teams (2026 Guide)
Choosing a web application pentesting provider can be difficult in a crowded market. This guide breaks down the leading vendors for SaaS teams and shows security leaders how to identify high-risk gaps, compare testing approaches, and select a partner that aligns with both engineering and compliance goals.
Modern SaaS products evolve constantly, adding new features, integrations, endpoints, and dependencies. This creates a moving attack surface that is difficult to understand (let alone defend) without continuous verification. One practical way to frame “what attackers are likely to try” is to align your program to the most common, consensus web app risk categories. The OWASP Top 10 explicitly enumerates the major risk areas SaaS teams repeatedly trip over.
For example:
- Broken Access Control
- Cryptographic Failures
- Injection
- Insecure Design
- Security Misconfiguration
- Vulnerable and Outdated Components
- Identification and Authentication Failures
- Software and Data Integrity Failures
- Security Logging and Monitoring Failures
- Server-Side Request Forgery (SSRF)
Broken Access Control remains the top category. The OWASP risk description emphasizes that access control failures lead to unauthorized disclosure or modification and allow users to act beyond their intended permissions.
Regulated and customer-audited SaaS environments are increasingly treating independent testing as table stakes rather than a luxury. As one concrete example, PCI DSS v4.0 contains explicit expectations for penetration testing (internal and external testing at least every 12 months and after significant changes, using qualified testers with organizational independence). It includes additional expectations for multi-tenant service providers to support customers’ needs for evidence of external penetration testing or access.
How web app testing methods fit together in practice
SaaS security leaders often inherit a “tool zoo” but lack a coherent verification strategy. The goal is to combine complementary testing methods so that each closes a known blind spot of the others, and so results become defensible evidence of risk control. This is the core intent behind widely used community testing methodologies, such as the OWASP Web Security Testing Guide (WSTG), which is positioned as a comprehensive, best-practice framework for penetration testers and organizations globally.
Static testing (SAST)
SAST finds problems by examining code without running it. The OWASP DevSecOps Guideline describes static code analysis as examining code “without executing the program” and notes that it can identify security vulnerabilities and programming errors. This fits naturally into pull requests and CI because it scales with engineering workflows and provides early feedback (when the developer still has full context). The same guidance also highlights that improved static coverage often includes dependency scanning (SCA) and even infrastructure-as-code scanning, because modern SaaS risk frequently arises from third-party code and configuration.
Dynamic testing (DAST)
DAST probes the running application from the outside (black-box testing). OWASP’s DevSecOps Guidance defines DAST as black-box testing against a running app, using injected payloads to identify flaws that enable attacks such as SQL injection or XSS, and notes its usefulness for issues like authentication problems and server configuration mistakes. This makes DAST especially valuable for SaaS teams because many real incidents come from runtime behaviors—misconfigurations, broken authentication flows, insecure headers/cookies, and API authorization bugs that are invisible to a purely code-centric view.
Interactive testing (IAST)
IAST aims to bridge the “code vs. runtime” gap by observing the app while it is being exercised. OWASP describes IAST as testing the application while it is running under automated tests, human testers, or other interactive activities. In SaaS, this often maps well to end-to-end test suites in staging because you can couple real user journeys (login, billing, admin actions, data export) with security observation.
Penetration testing
Pentesting adds the human, adversarial element by testing how weaknesses chain together in realistic attack paths, including business logic and multi-step exploitation. NIST describes penetration testing as security testing in which assessors mimic real-world attacks to circumvent security features, often launching actual attacks using attacker-like tools and techniques, and looking for combinations of vulnerabilities that yield more access than a single flaw.NIST also cautions that penetration testing is labor-intensive, requires expertise, carries risk to systems, and therefore demands careful consideration and planning.
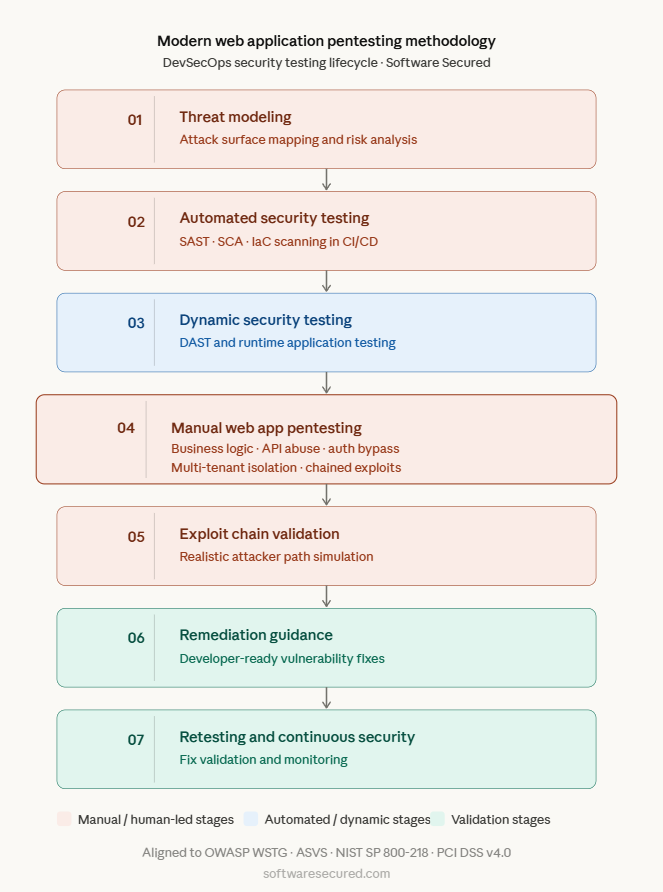
Designing a SaaS testing program that scales with CI/CD and reduces blind spots
High-performing SaaS security programs do not treat testing as an annual event. They treat it as an engineering system: risk modeling defines where to focus; automation checks every change; expert validation confirms what is truly exploitable; and monitoring continuously verifies the effectiveness of control.
A useful “north star” is the Secure Software Development Framework (SSDF). In SP 800-218, NIST explicitly recommends integrating secure development practices into each SDLC implementation. Within that framework, the SSDF emphasizes risk modeling, explicitly naming threat modeling, attack modeling, and attack surface mapping as a way to assess software security risk and guide mitigations. This is exactly how you prevent SaaS security work from becoming a series of random acts of tooling.
From a practical program-design perspective, SSDF is valuable because it treats testing as a portfolio of verification mechanisms, not one tool:
- It calls for conducting code review and/or code analysis (including static analysis) to identify vulnerabilities before release; it notes that automated methods reduce the effort and resources required to detect vulnerabilities.
- It calls for executable code testing and provides concrete examples such as integrating dynamic vulnerability testing into automated test suites, incorporating regression tests for prior vulnerabilities, using fuzz testing tools for input handling, and (where resources allow) using penetration testing for high-risk scenarios.
- It also points to ongoing vulnerability discovery (for example, gathering information from public sources and reviewing code to identify previously undetected vulnerabilities), reinforcing that SaaS security is continuous rather than episodic.
For SaaS teams, one of the most effective ways to cut through ecosystem noise is to turn a standard into a shared contract between engineering, security, and (later) external testers. The OWASP Application Security Verification Standard explains that ASVS provides a basis for testing web application technical security controls, gives developers a list of secure development requirements, and can be used as a metric, as guidance, and during procurement to specify verification requirements. That procurement angle matters: it lets you write pentest scopes and security acceptance criteria as plain, testable requirements rather than relying on vague “best effort” statements.
Finally, if your SaaS leadership cares about audit readiness and “confidence,” you should connect application testing to continuous monitoring. NIST SP 800-137 defines information security continuous monitoring as maintaining ongoing awareness of security, vulnerabilities, and threats to support organizational risk management decisions, and it emphasizes metrics and actionable communication across the organization.
Identifying high-risk gaps using attacker realism, not tool checklists
SaaS security leaders typically discover painful gaps in three predictable ways: a customer questionnaire triggers an uncomfortable audit conversation, a production incident exposes missing controls, or an external pentest finds issues your tools never flagged. A better approach is to target the gaps attackers exploit most and to ensure each gap has at least one strong detection mechanism and one strong validation mechanism.
A risk-informed gap assessment should start by mapping your architecture (web app + APIs + identity + configuration + dependencies) to today’s consensus risk categories:
- Access control and authorization brittleness.
- API-specific authorization failures.
- Injection-class attacks.
- Misconfiguration and weak operational controls.
- Detection gaps and incident visibility.
A key misconception in crowded security testing ecosystems is believing that “running scans” equals “having assurance.” PCI DSS explicitly states that scanning for vulnerabilities alone is not a penetration test, and it describes penetration testing as highly manual, even when automated tools are used, because the tester chains exploits to break through layers of defense in a way that better simulates attacker techniques. OWASP’s DAST tooling guidance makes a similar point: while DAST can be automated, manual assessment is still important for issues that automated tools miss (including business logic errors).
What to Look for in Web Application Penetration Testing Services
For SaaS leaders, the “right” penetration test is not the cheapest scan-and-report. It is an engagement that:
- Tests the paths attackers would actually use in your product
- Produces findings your engineers can act on quickly
- Yields evidence that leadership and auditors can trust.
A strong baseline is to demand that the provider’s methodology aligns with well-established guidance. From a SaaS governance standpoint, PCI DSS v4.0 gives unusually concrete selection signals that can be repurposed even outside payment environments. It states that both internal and external penetration testing should be performed according to a defined methodology at least once every 12 months and after significant infrastructure/application changes.
For multi-tenant SaaS specifically, PCI DSS adds a requirement for multi-tenant service providers to support customers' external penetration testing needs (either by providing evidence that comparable testing was performed or by providing access so customers can test). Even if you are not in PCI scope, this is a powerful “trust signal” benchmark: customers increasingly expect either evidence or safe mechanisms to validate isolation boundaries in shared environments.
When security leaders say “we need practical advice,” it often means: *what do we ask, and what answers indicate they’ll actually help us?* The following questions are tightly grounded in what NIST, PCI DSS, and FedRAMP describe as necessary for real penetration testing governance:
- How do you define and document ROE, scope, assumptions, limitations, and risk controls? NIST provides an ROE template structure that explicitly includes purpose, scope, assumptions/limitations, risks, personnel, and test schedule/logistics.
- How will you test both outsider and insider perspectives (where appropriate), and how do you avoid accidental cross-tenant impact? PCI DSS distinguishes testing between inside and outside the network, while FedRAMP emphasizes boundary management and constraints.
- How do you handle critical findings during the engagement? FedRAMP requires rapid notification of critical/high-impact vulnerabilities to appropriate leadership roles (not weeks later in the final report).
- What is your retest/validation approach after remediation? PCI DSS expects verification that exploitable vulnerabilities and weaknesses discovered during penetration testing are corrected and that testing is repeated to verify corrections.
- How do you differentiate “scan output” from attacker-realistic exploitation paths? PCI DSS explicitly states that scanning alone is not pen testing and describes that pen testing often chains vulnerabilities to break through defenses.
- How will you connect findings to a defined risk taxonomy (for example, today’s OWASP Top 10 categories) and to your environment’s real controls? OWASP’s Top 10 categorization is a widely used awareness baseline, and PCI DSS also expects testing aligned to defined methodologies and threat considerations.
If the provider cannot give crisp, documented answers to these questions up front, the engagement is likely to devolve into either.
(a) shallow scanning
(b) interesting exploitation stories that your team cannot reproduce and remediate effectively.
Why Listen to Us
The recommendations in this guide are grounded in over a decade of hands-on penetration testing experience, conducted exclusively within SaaS environments, and built on a methodology that aligns with the most rigorous security standards in the industry.
Since 2010, we have worked exclusively with SaaS companies; not governments, not retail chains, not manufacturing OT environments. That narrow focus means our team has deep institutional knowledge of the specific vulnerability patterns, multi-tenancy risks, API authorization failures, and token-handling errors that appear repeatedly in SaaS architectures. When we evaluate the vendors on this list, we apply the same technical lens we use in our daily production engagements.
10 Leading Web Application Penetration Testing Providers
Software Secured has operated since 2010 with a singular focus: delivering high-impact manual penetration testing for SaaS companies. Unlike platform-first PTaaS vendors, Software Secured operates with a full-time team of Canadian security professionals who perform every test manually. This is a consultancy built around depth, remediation quality, and developer-level collaboration rather than speed or self-service scale.
Key Features & Services
- Manual web application, API, and mobile penetration testing targeting business logic flaws, authorization bypasses, and chained exploits that automated scanners cannot detect
- External and internal network penetration testing covering perimeter exposure, lateral movement paths, and privilege escalation opportunities
- Secure cloud review assessing AWS, Azure, and GCP environments for misconfigurations, excessive permissions, and insecure trust relationships
- AI, IoT, and hardware security testing, including prompt injection, weak firmware, and side-channel vulnerabilities
- Penetration Testing as a Service (PTaaS) provides ongoing manual testing aligned to release cycles, with unlimited retesting and native integrations into Jira, Linear, Azure DevOps, Slack, Drata, and Vanta.
- Software Secured Portal for real-time finding visibility, SLA tracking, remediation workflow management, and component-level compliance reporting, shareable directly with auditors and customers
- Compliance-mapped reporting for SOC 2, ISO 27001, PCI DSS v4.0, HIPAA, and GDPR — structured to serve both engineers and auditors from a single engagement deliverable
Pros
- Fully manual methodology delivers maximum depth for business logic flaws and application-specific vulnerabilities.
- A developer-friendly communication style makes findings immediately actionable for engineering and product teams.s
- Transparent, fixed pricing removes budget uncertainty
- Unlimited retesting included
- Deep SaaS specialization means testers understand multi-tenant architectures, API chains, and token-based auth patterns.ns
Cons
- Smaller team limits availability and engagement concurrency — not suited for organizations needing multiple parallel tests.sts
- No automated scanning layer means less breadth velocity compared to hybrid platforms.
- Primarily serves the North American market; international regulatory compliance depth may be limited.
- Not the right fit if continuous or always-on coverage is a priority beyond scheduled retesting windows
Pricing
Fixed, transparent pricing: Starting at $10,800 USD
2. NCC Group
Founded in 1999 and headquartered in Manchester, UK, NCC Group is one of the world's most recognized cybersecurity firms, with offices across North America, Europe, Asia-Pacific, and Australia. Their penetration testing practice is built entirely around full-time, certified security consultants. NCC Group is the default choice for government agencies, large financial institutions, and global enterprises where audit-grade assurance and independence are non-negotiable. For SaaS teams handling sensitive regulated data or entering enterprise sales cycles, NCC Group's reports carry significant weight with auditors and procurement teams.
Key Services
- Expert-led manual web, mobile, and native application penetration testing with a consultant-led engagement model from scoping through to delivery
- Network and infrastructure penetration testing covering both external perimeter and internal lateral movement scenarios
- Cloud security assessments across AWS, Azure, and GCP — including IaaS, PaaS, SaaS layers, containers (Docker, Kubernetes), and serverless functions
- Architecture reviews and threat modeling are integrated into application security engagements.
- Red team and adversary simulation exercises for mature security programs
- Hardware and IoT security testing for organizations with embedded or physical attack surfaces
- Hybrid testing option combining manual consultant expertise with the NodeZero® AI platform (via their Horizon3.ai partnership) for network-layer efficiency
- Compliance-aligned reporting for PCI DSS, HIPAA, SOC 2, ISO 27001, GDPR, and FedRAMP
Pros
- Over 25 years of unmatched institutional expertise
- Full-time, globally distributed team of certified professionals (CREST, OSCP, CHECK)
- Covers the broadest technology scope of any vendor on this list: applications, cloud, network, hardware, and IoT
- Deep compliance and regulatory expertise make audit deliverables highly authoritative
- Strong strategic advisory layer that elevates findings beyond a vulnerability list into a business risk context
Cons
- Premium pricing places engagements at the higher end of the market
- Engagement timelines tend to be longer than PTaaS platforms due to consultancy scoping and scheduling processes
- Breadth of services can add overhead for SaaS teams that only need focused web application or API testing
- Less optimized for high-frequency, CI/CD-integrated testing
Pricing
Fully custom, quote-based pricing. Engagements typically range from $20,000 to $100,000+, depending on scope, service type, and regulatory complexity.
Trail of Bits is a New York-based cybersecurity firm recognized as a Forrester Wave Leader in Cybersecurity Consulting Services (Q2 2024). Founded by world-class security researchers, the firm occupies a unique position: it operates at the intersection of offensive security, formal verification, and custom tooling. For SaaS teams with cryptographic implementations, complex authentication architectures, or proprietary protocol layers, Trail of Bits brings a caliber of analysis that few firms can replicate.
Key Services
- Manual web application and network penetration testing with a focus on deep code-level and logic analysis
- Secure code review and source-level vulnerability research using static analysis, fuzzing, and formal verification techniques
- Blockchain and smart contract security audits: a recognized world leader in this domain (Ethereum 2.0, Uniswap, Compound)
- Custom security tool development for clients requiring proprietary detection or exploitation tooling
- Cryptography review for applications implementing custom or non-standard cryptographic schemes
- Software assurance consulting covering threat modeling, secure SDLC integration, and architectural risk review
- Training and advisory services helping engineering teams internalize security practices at the code level.
Pros
- Research-grade manual analysis that goes significantly deeper than standard pentest playbooks
- Team composed of world-class security engineers who regularly discover novel vulnerability classes in hardened systems
- Formal verification and custom tooling capabilities are unique differentiators unavailable at most testing firms.s
- Proven track record with some of the world's most security-sensitive organizations and products
- End-to-end SDLC coverage
Cons
- Premium pricing reflects the seniority and research depth of the team — not suited for routine annual compliance tests.
- Smaller team relative to global consultancies; engagement availability can be constrained for large or multi-scope programs.
- Less emphasis on compliance-driven deliverables and audit-ready report formats compared to firms like Coalfire or NCC Group
- Not a platform or PTaaS offering — pure consultancy with associated lead times and scoping overhead
- Overkill for standard web application assessments that don't involve cryptography, complex protocols, or hardened codebases
Pricing
Custom, quote-based pricing with flexible models based on scope and engagement type. Typical engagements range from $25,000 to $150,000+, with research-grade or multi-phase engagements at the higher end.
4. Bishop Fox

Bishop Fox is one of the largest firms dedicated exclusively to offensive security. Their brand is built on a "research-driven offensive security DNA" — their consultants develop widely used open-source attack tools (including Sliver, a leading C2 framework), publish cutting-edge vulnerability research, and conduct adversary simulations for Fortune 500 companies and clients in high-security sectors. Bishop Fox provides a rare combination of deep manual testing expertise and enterprise-grade delivery processes, making it suitable for SaaS organizations where application security intersects with complex cloud infrastructure, sensitive regulated data, or high-value IP.
Key Features & Services
- Expert-led manual web application and API penetration testing, including multi-step business logic and authorization chain attacks
- Red team and adversary emulation exercises simulating APT (Advanced Persistent Threat) tactics, techniques, and procedures (TTPs)
- Cloud-native security testing across AWS, Azure, and GCP — including serverless, Kubernetes, and microservice attack paths
- Continuous attack surface management through their proprietary CAST platform, providing ongoing external exposure monitoring between point-in-time tests
- Secure code review and threat modeling integrated with pentest engagements
- AI and LLM security testing — a growing service line addressing prompt injection, model extraction, and inference attacks in AI-enabled SaaS products
- Compliance-aligned deliverables for SOC 2, FedRAMP, PCI DSS, and HIPAA
Pros
- Among the deepest offensive expertise available, the team regularly discovers novel, high-impact vulnerabilities in hardened environments.
- Research-driven methodology ensures testing techniques stay ahead of commodity tooling and scanner coverage.e
- Highly organized, enterprise-grade engagement process with minimal client-side overhead
- The CAST platform extends value between engagements through continuous attack surface visibility.
- Strong track record in complex, multi-tier SaaS and cloud-native architectures
Cons
- Among the highest-cost providers in the market, engagement budgets are typically enterprise-level
- Longer engagement timelines and scheduling lead times are given, given the caliber of staff assigned.
- Less optimized for high-frequency, rapid-turnaround testing cycles aligned with aggressive CI/CD release schedules
- Can be disproportionate for straightforward web application assessments without advanced threat modeling needs
Pricing
Custom, quote-based. Typical engagements range from $25,000 to $150,000+, depending on scope, service type, and whether red team or continuous ASM components are included.
5. Rapid7
Rapid7 is a Boston-based cybersecurity platform company founded in 2000, serving over 7,200 organizations across 120 countries. While widely known for its vulnerability management (InsightVM) and SIEM (InsightIDR) platforms, Rapid7 maintains a substantial global professional services division that delivers manual penetration testing and red teaming engagements. The primary value proposition for SaaS teams is integration: pentest findings feed directly into the Insight platform, eliminating the data silo between point-in-time test results and continuous vulnerability management operations.
Key Features & Services
- Manual web application and network penetration testing delivered by Rapid7's professional services team
- InsightAppSec (DAST) for continuous automated application scanning, complementing manual engagements
- Red team operations and adversarial simulation for mature security programs
- Managed Detection and Response (MDR) that can run in parallel with testing engagements
- Metasploit Pro for internal red team validation workflows — one of the most widely used exploitation frameworks in the industry
- InsightVM for continuous post-test vulnerability management, maintaining visibility between engagements
- Compliance-ready deliverables mapped to PCI DSS, HIPAA, SOC 2, and ISO 27001
Pros
- Deep integration between manual pentest findings and the broader Insight platform (VM, SIEM, SOAR) eliminates reporting silos.
- Mature, enterprise-grade reporting with clear remediation prioritization tied to business risk
- Broad service and product portfolio covers the full security lifecycle — a single vendor relationship for testing, monitoring, and response.e
- Strong compliance pedigree and an established client base across finance, healthcare, and technology
Cons
- Manual penetration testing is not Rapid7's primary business — platform products are the core; testing is a services add-on.
- Less agile than PTaaS-native providers; engagements are not optimized for high-frequency or rapid-turnaround testing cycles.
- Pricing scales quickly, particularly when combining platform licensing with professional services engagements
- Testing depth for complex web applications or API assessments may not match specialist firms like Bishop Fox or NCC Group.
Pricing
InsightAppSec (automated) starts at approximately $2,100 per application per year. Manual professional services engagements are custom-priced; typical ranges are $15,000–$60,000+ per engagement, depending on scope.
6. Cobalt.io
Cobalt.io pioneered the Penetration Testing as a Service (PTaaS) model and remains the most recognized practitioner of it. While the platform handles delivery, scoping, reporting, and workflow integration, the actual security testing is performed entirely by human testers from a community of 450+ vetted security researchers. This distinction matters: Cobalt's model is not automated scanning with a human review layer, but genuine manual testing conducted by qualified practitioners, with a platform layer that accelerates coordination and the delivery of findings. For SaaS teams running CI/CD pipelines, Cobalt provides the manual depth needed to catch logic flaws and chained exploits while operating at the speed of modern engineering.
Key Features & Services
- Manual web application, API, mobile, and network penetration testing by vetted researchers with skill-matched assignments
- Real-time findings delivery via a collaborative dashboard — findings are surfaced as discovered, not held until the final report.
- Direct tester collaboration via Slack or in-app messaging throughout the engagement
- CI/CD and Jira integrations enabling findings to flow directly into developer ticketing and sprint workflows
- DAST (Dynamic Application Security Testing) automated scanning as a complement to manual engagements
- Compliance-ready reporting mapped to SOC 2, PCI DSS, ISO 27001, and HIPAA
- Flexible credit-based pricing model allowing spend to be distributed across multiple test types and timelines
Pros
- Fastest test launch time in the market; tests can kick off in under 24 hours from scoping
- Strong DevSecOps alignment
- Transparent real-time visibility into test progress and individual vulnerability findings
- Large, geographically diverse researcher pool enables skill-matched engagement for specialized technology stack.s
- A Crowdsourced model that provides a breadth of attacker perspectives that a single-team firm cannot replicate
Cons
- Tester consistency can vary between engagements.
- Less suited to organizations needing a single dedicated expert team with deep, accumulated context about the application architecture
- A credit-based pricing model can be difficult to budget predictably when testing needs evolve across quarters.s
- Business logic and complex, chained exploit coverage depend on the depth of the matched researcher.
Pricing
Custom, credit-based pricing. Mid-market engagements typically fall in the $10,000–$30,000 range per engagement, depending on scope and researcher hours.
7. NetSPI
NetSPI is a Minneapolis-based enterprise offensive security firm with over 300 in-house security professionals. It delivers expert-led manual penetration testing through its proprietary Resolve™ PTaaS platform, which centralizes test management, real-time finding delivery, and remediation tracking. NetSPI occupies the premium end of the PTaaS market — combining the platform efficiency of a SaaS delivery model with the depth and consistency of a full-time, in-house testing team. It is the go-to choice for Fortune 500 companies, major financial institutions, and healthcare organizations requiring both high-assurance manual testing and compliance-grade documentation.
Key Features & Services
- Deep manual penetration testing across web applications, APIs, networks, cloud (AWS, Azure, GCP), containerized workloads, and serverless functions
- Resolve™ platform for centralized test orchestration, SLA tracking, real-time finding delivery, and compliance evidence management
- Cloud security assessments covering IAM exploitation, container escape paths, lateral movement in cloud-native environments, and misconfiguration identification
- Attack surface management (ASM) is integrated with testing programs for continuous external exposure monitoring.
- Red team and adversary simulation for mature security programs requiring full-scope TTPs
- Advisory services for embedding security findings into long-term program roadmaps
- Comprehensive compliance-ready reporting for SOC 2, PCI DSS, HIPAA, and NIST frameworks
Pros
- Testers are known for uncovering complex, chainable attack paths
- High-touch engagement model with multiple structured check-ins and a consultative relationship throughout.
- Resolve™ platform is consistently praised as a one-stop portal for all test management, remediation tracking, and retesting.
- Strong remediation guidance and formal retesting cycles ensure fixes are properly validated.
- A full-time in-house team provides engagement consistency and institutional quality that crowdsourced models cannot match.
Cons
- Premium pricing is not suited for smaller SaaS budgets
- Engagement onboarding and scoping timelines can be longer than agile PTaaS platforms
- Primarily oriented toward large enterprises, the engagement model may carry unnecessary overhead for simpler, bounded SaaS assessments
- Less optimized for high-frequency, rapid-turnaround tests tied to individual sprint cycles
Pricing
Custom, enterprise pricing. Engagements typically range from $20,000 to $100,000+, depending on the scope of assets, service type, and the depth of required compliance documentation.
8. Coalfire

Coalfire is a Colorado-based cybersecurity advisory firm founded in 2001, recognized as one of the leading third-party assessors for compliance-heavy frameworks in the United States and globally. Their penetration testing practice, operated through the DivisionHex cybersecurity services division, takes an adversarial, threat-informed approach to manual testing — but uniquely contextualizes every finding in the context of the client's compliance obligations. Coalfire is the leading FedRAMP Third Party Assessment Organization (3PAO), making it the natural choice for SaaS companies pursuing federal market access. For any SaaS organization where penetration testing is not just a security exercise but an audit deliverable, Coalfire's combination of testing rigor and compliance expertise is a significant advantage.
Key Features & Services
- Manual application penetration testing (web, mobile, APIs) and network penetration testing via the DivisionHex team
- Red team operations and adversarial emulation simulating sophisticated threat actor TTPs
- Application security assessments, including threat modeling, SAST/DAST integration, and secure SDLC advisory
- FedRAMP penetration testing and red team services
- Compliance-integrated testing for PCI DSS, SOC 2, HIPAA, ISO 27001, FedRAMP, FISMA, CMMC, and DoD RMF
- Generative AI and LLM security testing — an emerging service for SaaS teams deploying AI-powered features
- Hexeon platform for engagement management, vulnerability remediation tracking, and compliance evidence collection
- Dark web monitoring, vulnerability management, and attack surface management as program-level add-ons
Pros
- UReports are designed for auditors and satisfy the evidence requirements of multiple frameworks simultaneously
- Leading FedRAMP 3PAO designation makes Coalfire the top choice for SaaS teams entering the federal and government market
- 70% of high-severity vulnerabilities are detected by trained experts, not automated tools, per their own data
- Broad service portfolio covers the full security lifecycle, reducing the number of vendor relationships needed
- Strong client base across regulated industries: healthcare SaaS, fintech, federal contractors, and enterprise software
Cons
- Compliance orientation means the primary deliverable lens is regulatory alignment.
- Premium pricing, particularly for FedRAMP-level engagements
- Less optimized for high-velocity DevSecOps environments or CI/CD-integrated continuous testing
- The engagement model is consultancy-heavy
Pricing
Custom, quote-based pricing. Standard web application penetration testing engagements typically range from $15,000 to $50,000.
9. Synack
Synack is a globally distributed, highly vetted network of elite ethical hackers who are background-checked and continuously assessed. Unlike open bug bounty programs, Synack's SRT is a curated, controlled environment. Their proprietary AI-enhanced platform automates reconnaissance and initial attack surface mapping, freeing human researchers to concentrate exclusively on complex, high-impact vulnerabilities that require manual reasoning. Synack offers a continuous testing model and an outcome-based engagement option in which organizations pay for validated vulnerabilities rather than for researcher time.
Key Features & Services
- SRT (Synack Red Team): Access to a curated global pool of elite, vetted security researchers — not an open public community
- AI-enhanced reconnaissance that feeds human testers with prioritized targets, reducing wasted effort on known surface
- Continuous testing model providing always-on coverage rather than isolated point-in-time assessments
- Web application, API, mobile, and network manual penetration testing with custom scoping
- Attack surface management with ongoing asset discovery integrated into the testing workflow.
- Outcome-based engagement option where payment is tied to validated, severity-weighted findings
- Compliance-aligned reporting with findings mapped to OWASP, NIST, and relevant regulatory frameworks
Pros
- Scale and diversity of attacker expertise that a single-team firm cannot replicate
- Continuous model provides persistent coverage aligned with fast SaaS release and deployment cycle.s
- AI-assisted recon significantly expands the attack surface covered per engagement dollar.
- Remediation teams receive actionable results, not noise
- Outcome-based pricing option aligns vendor incentives directly with finding quality
Cons
- One of the most expensive options on this list, annual contracts can reach $230K
- Less consultative than firm-based providers; depth in remediation advisory is limited compared to NCC Group or Coalfir.e
- A crowdsourced model may lack the accumulated business context about your application that a dedicated long-term team would develop. op
- Less suited for organizations primarily needing compliance-driven, structured, single-report deliverables for auditors
Pricing
Contracts typically range from $30,000 to $230,000, with an average of around $86,000/year.
10. BreachLock
BreachLock was founded in 2018 and operates as a cloud-based Penetration Testing as a Service (PTaaS) platform that combines AI-powered automated scanning with a dedicated team of certified manual penetration testers. The manual testing component is not an afterthought — BreachLock employs a dedicated team of expert reviewers who validate automated findings, pursue logic-layer and chained-exploit paths, and provide the human attacker's perspective that scanners cannot replicate. This hybrid model is designed to deliver the accuracy and depth of manual testing at the operational efficiency and price point of a platform-based service.
Key Features & Services
- Dedicated manual penetration testing by a certified in-house team for web applications, APIs, mobile apps, cloud environments (AWS/Azure/GCP), networks, and IoT
- Hybrid VAPT methodology combining automated baseline scanning with manual expert validation to maximize both coverage and depth
- Continuous testing model with monthly automated scans running between scheduled manual assessments
- Compliance-driven reporting covering SOC 2, PCI DSS, ISO 27001, HIPAA, and GDPR with audit-ready documentation
- SaaS portal for real-time finding access, remediation workflow tracking, and retesting requests
- Retesting included post-remediation to validate that identified vulnerabilities have been properly addressed.
- DevOps integrations connecting the portal to ticketing and CI/CD tooling
Pros
- A dedicated manual tester team provides more consistency than crowdsourced platforms.
- The hybrid model delivers strong coverage efficiency
- Predictable, fixed pricing makes budget planning straightforward
- Strong compliance reporting
- Monthly automated scans between manual assessments provide continuous baseline visibility at no additional cost.t
Cons
- Manual testing depth for the most complex enterprise architectures may not match premium consultancies like NetSPI or Bishop Fox
- A platform-first model means a less direct consultative relationship compared to a full-service firm.ms.
- AI-first baseline scanning requires careful human review to ensure context-dependent business logic flaws are not missed in the automated pass.
- Less suited for organizations with complex multi-cloud, multi-region infrastructure requiring very deep cloud security expertise
Pricing
Web application penetration testing engagements typically start around $7,500–$15,000, with continuous subscription programs and enterprise custom pricing available.
Pentesting Vendor Evaluation Guide
Choosing a pentesting provider can be difficult, espapplications, APIs, mobile apps, cloud environments (AWS/Azure/GCP), networks,ecially when many vendors claim similar capabilities. To help SaaS security leaders make more informed decisions, check out this Pentesting Buyers Guide that includes:
- The questions you should ask pentesting vendors
- How to evaluate manual vs automated testing
- How to compare PTaaS platforms vs consulting firms
- What strong reporting and remediation guidance should look like
Why Software Secured is the #1 choice for web app testing and reporting
Generic penetration testing frameworks enumerate vulnerabilities. Software Secured's SaaS-focused testing starts from a different question: how does an attacker move through this specific application to reach something that matters? The answers are almost always SaaS-specific:
- Multi-tenant data isolation failures: where a properly authenticated user in one tenant can enumerate, read, or modify records belonging to another. These are logic-layer vulnerabilities that no scanner can detect because the application returns an HTTP 200 response with valid-looking data.
- Broken object-level and function-level authorization in APIs: the top two categories in the OWASP API Security Top 10, and endemic in SaaS products with complex role hierarchies, delegated admin models, and multi-step workflows.
- Token and session boundary abuse: including JWT algorithm confusion, OAuth implicit flow misuse, insufficient scope validation, and cross-tenant session fixation patterns arising from shared-infrastructure SaaS architectures.
- Business logic exploitation: privilege escalation through subscription-tier abuse, feature-flag bypass, workflow-step skipping, and price manipulation, all of which require a tester who understands your product model, not just your HTTP traffic.
Software Secured uses a testing methodology that maps every engagement to the OWASP WSTG and ASVS Level 2 as a baseline, with Level 3 controls applied to authentication, session management, and access control components. These are the areas where SaaS applications most frequently fail under adversarial pressure.
The vendors ranked #2 through #10 on this list are strong providers with legitimate use cases. If your organization is pursuing FedRAMP authorization, Coalfire's 3PAO designation makes it the functionally correct choice. If you are assessing a cryptographic protocol implementation, Trail of Bits operates in a different technical tier. If you need to run fifty parallel tests across a large enterprise asset inventory, NetSPI's platform is built for that scale.
Software Secured is the right choice when your priority is maximum testing depth on a SaaS web application, delivered by a team that has spent fifteen years doing exactly that, with pricing that does not require an enterprise security budget, reporting that your engineers will actually act on, and a retesting model that keeps working until the vulnerabilities are gone.
If that is the problem you are trying to solve, Software Secured is the most direct path to solving it.



.avif)

