Top 10 Cloud Security Assessment Companies for SaaS (2026 Guide)
This guide explains why proactive cloud security reviews have become a critical step for SaaS security leaders. It breaks down the most common cloud misconfiguration patterns, lessons from major breaches, and the practical controls security teams should evaluate across identity systems, infrastructure, CI/CD pipelines, and monitoring environments.
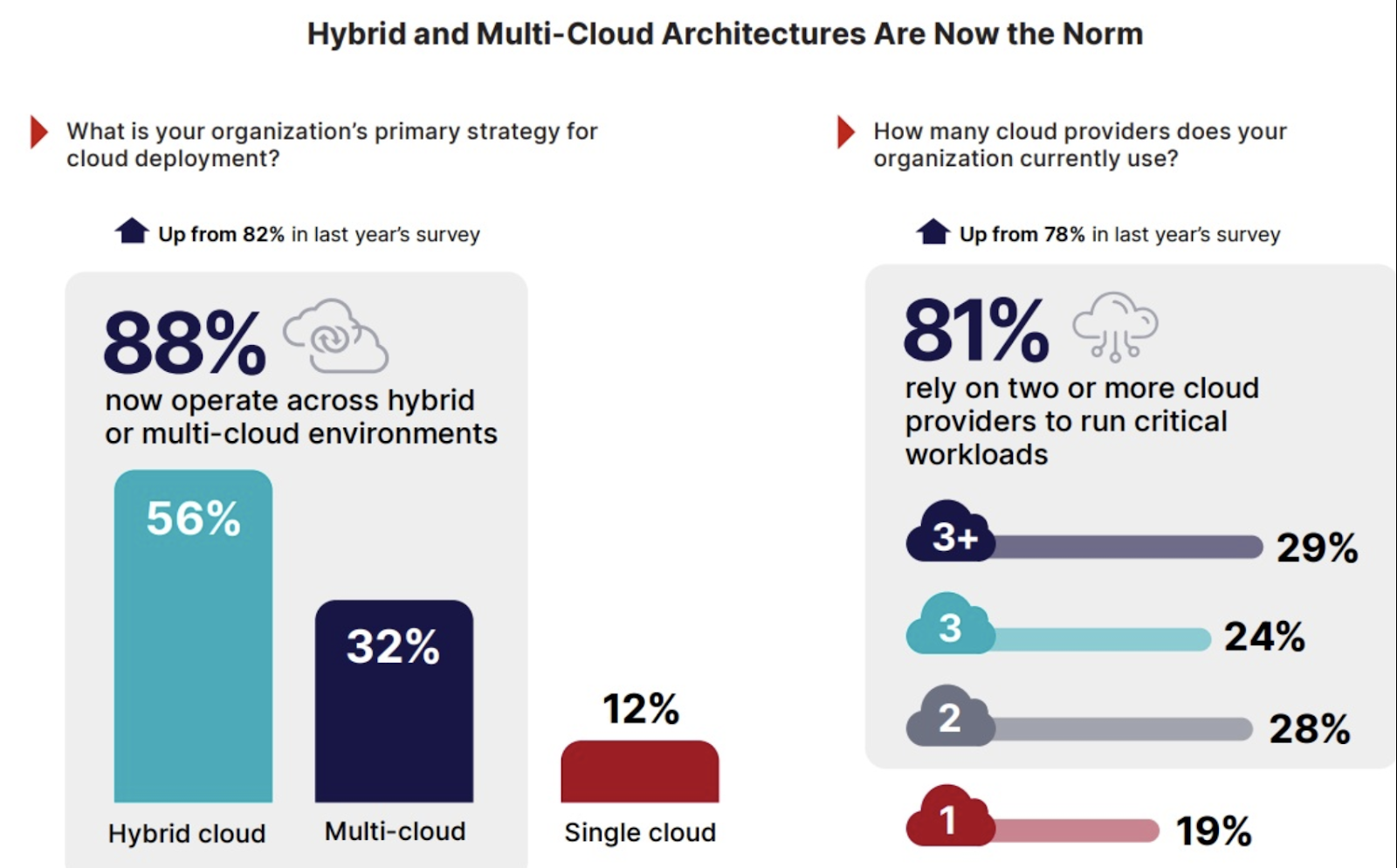
As organizations enter 2026, cloud complexity is increasingly outpacing human defenses, with 88% of organizations now operating in hybrid or multi-cloud environments. The attack surface has expanded, making visibility and consistent security more difficult to maintain. A secure cloud review has therefore become a critical IT priority to manage the rising risks of identity breaches, misconfigured services, and data exposure.
A comprehensive secure cloud review encompasses two distinct but complementary processes: cloud security assessments and cloud security audits.
- Assessments are proactive, technical evaluations designed to identify vulnerabilities and gaps in specific applications or configurations. They often use expert-led penetration testing and automated scanners to surface security flaws.
- Audits take a broader view by systematically verifying that an organization’s entire infrastructure, policies, and controls comply with industry regulations and standards such as GDPR, HIPAA, or PCI DSS.
The foundation of any secure cloud review is a shared responsibility model. Cloud service providers (CSPs) are responsible for the security of the cloud, the underlying infrastructure, while the organization is responsible for security to, from, and in the cloud, including its own data, workloads, and access management.
Most organizations already use CSPM or automated security tools, which provide valuable continuous monitoring. A secure cloud review complements them by validating whether the environment actually behaves the way security teams believe it does, uncovering risks that automated rules or dashboards may miss. By balancing automation and technical assessments with compliance-driven audits, organizations can navigate the evolving threat landscape and lead their digital transformations with confidence.
SaaS companies face a unique risk profile that makes cloud security reviews more urgent than for traditional enterprises
- Multi-tenancy means that a single misconfiguration can expose data to thousands of customers simultaneously.
- Continuous deployment cycles create a new attack surface on every release.
- Investor and enterprise customer due diligence now routinely includes cloud security attestation.
- SOC 2 Type II auditors are increasingly sampling cloud configurations directly instead of just reviewing policies.
Common patterns that repeatedly drive SaaS cloud incidents
These high-frequency failure modes show up across modern incident reporting:
CircleCI 2023
CI/CD and SaaS token blast radius: In the incident report, the company describes malware on an engineer’s laptop that stole a valid SSO session cookie, enabling escalation to production systems, prompting broad token rotation/revocation guidance for customers. A secure cloud review would explicitly test “developer endpoint compromise → CI secrets → production access,” and would flag high-value tokens with excessive scope, weak segmentation between CI and production, and lack of rapid token revocation playbooks.
Okta 2023
Support artifacts and logging blind spots: A threat actor accessed files in its customer support system (including HAR files with session tokens), and initial investigations missed suspicious downloads due to gaps in log event interpretation; remediation included disabling the service account, blocking personal Google profile sign-in on corporate devices, and enhanced monitoring. A secure cloud review would include support artifacts in scope, test token leakage pathways, and validate that logs are complete and interpretable for investigations.
Microsoft 2023
Key management and “catastrophic” identity compromise: Storm-0558 disclosures describe an acquired consumer signing key being used to forge authentication tokens and access email from about 25 organizations. Secure cloud reviews should treat signing keys, token validation paths, and key-handling processes as “crown jewels,” and explicitly verify separation, monitoring, and response playbooks for compromised keys.
Benefits of Getting it Right
Selecting a Secure Cloud Review partner
Partnering is often beneficial when internal teams lack time, specialized cloud attack-path expertise, or independent credibility for executives and customers. The key is to pick a partner whose methods produce verifiable control outcomes, not just a long list of findings.
A Checklist for Secure Cloud Review Vendor Selection
A partner worth hiring should be able to demonstrate, in writing, their answers to these points:
- Methodology: how they scope (including third parties), threat model, and risk-score; whether they align to recognized baselines like CIS and cloud-provider security frameworks.
- Evidence and retesting: whether every finding has configuration evidence, impact explanation, fix guidance, and a defined retest cycle with SLAs.
- Tooling and automation: whether they can operationalize IaC/policy-as-code, centralized logging, and continuous monitoring rather than producing a static report.
- Compliance alignment: ability to map findings to your obligations (SOC 2, ISO 27001, HIPAA, PCI DSS) and produce auditor-friendly evidence without “checkbox theater.”
- References and incident experience: whether they can cite comparable SaaS engagements and demonstrate incident learnings (token theft, CI compromise, logging gaps).
Why Listen to Us?
We have spent over a decade working exclusively with SaaS companies, navigating cloud risk, compliance pressures, and enterprise security scrutiny. We routinely investigate real-world attack paths, from CI/CD token misuse and IAM privilege escalation to serverless misconfiguration and logging blind spots. Our perspective is grounded in offensive testing, incident response exposure, and helping engineering teams remediate issues without derailing product velocity.
This guide reflects patterns we see repeatedly across SaaS cloud environments, based on hundreds of cloud security assessments and secure cloud reviews across AWS, Azure, and GCP.
Top 10 Secure Cloud Review Providers (2026 Comparison Guide)
Below is a structured breakdown to help you evaluate each vendor based on capability, depth, and fit.
1. Software Secured

Software Secured is a specialized manual penetration testing firm headquartered in Canada, focused exclusively on application and cloud security for SaaS companies and the technology sector. Unlike generalist consulting firms, Software Secured's cloud review practice is purpose-built for the SaaS environment: multi-tenant architectures, CI/CD pipelines, infrastructure-as-code, and the compliance requirements that come with enterprise sales motions.
Key Features & Services
- Manual cloud configuration review across AWS, Azure, and GCP
- IAM and privilege escalation path analysis (not just policy checklist)
- IaC security review (Terraform, CDK, Pulumi, CloudFormation)
- Secrets management and key rotation assessment
- Network architecture and perimeter review
- Compliance-mapped findings for SOC 2, ISO 27001, and HIPAA
- Retest of critical findings included in the base scope
- Executive summary formatted for board, investor, or enterprise buyer audiences
Pros
- Manual-first methodology catches logic flaws that automated tools miss
- Deep SaaS domain expertise: testers understand multi-tenancy risk
- Findings formatted for both engineering teams and compliance auditors
- Consistent quality from dedicated cloud specialists who run reviews and join calls
- Custom reports from their portal let you brand exports and control technical depth
- Fixed-scope, transparent pricing
Cons
- Smaller team than Tier 1 consulting firms, so there may be longer lead times during peak periods.
- Less geographic presence outside North America
- May not be the best fit for very large, complex multi-cloud enterprises needing staff augmentation
Pricing
Project-based fixed-scope pricing starting at 6,200$ USD.
Best Suited For
SaaS companies from seed through Series C seeking a rigorous, compliance-aligned cloud review with clear peer benchmarking and findings their engineering team can actually act on.
2. NetSPI
With over 300 in-house pentesters and CREST accreditation, NetSPI operates at a scale that is rare among manual-first firms. Their cloud penetration testing practice covers AWS, Azure, and GCP across the IaaS, PaaS, and SaaS layers, with a proprietary PTaaS platform that provides clients with real-time visibility into findings, retesting status, and remediation progress. Analysts consistently recognize NetSPI and serve large enterprise clients across financial services, healthcare, and technology sectors.
Key Features & Services
- Manual cloud configuration review across AWS, Azure, and GCP (IaaS, PaaS, SaaS layers)
- IAM and privilege escalation path analysis with custom tooling
- Container and Kubernetes security review
- Serverless function security assessment (Lambda, Azure Functions, GCP Cloud Run)
- Penetration Testing as a Service (PTaaS) platform with real-time findings and retest tracking
- Attack Surface Management (ASM) and External Attack Surface Management (EASM)
- Breach and Attack Simulation (BAS) with cloud-specific attack scenarios
- Compliance-mapped findings for SOC 2, HIPAA, PCI DSS, FedRAMP, and CMMC
Pros
- 300+ in-house testers provide depth and capacity that boutique firms cannot match
- A PTaaS platform gives clients live engagement visibility
- CREST accreditation and 2024 GigaOm leader recognition provide strong third-party validation
- Custom tooling for IAM and cloud-specific attack paths goes beyond standard methodology
- A broad compliance framework coverage suits heavily regulated enterprise clients
Cons
- Enterprise focus may mean less SaaS startup agility with high minimum engagement sizes
- A platform-first delivery model may feel impersonal compared to boutique consulting relationships
- Breadth of services could dilute specialist depth compared to cloud-only firms
Pricing
Project-based and subscription (PTaaS) models are available. Premium pricing tier reflecting enterprise scale.
Best Suited For
Mid-market to large enterprise organizations that need a high-capacity, credentialed offensive security partner with a mature delivery platform and broad cloud coverage.
3.TrustedSec
TrustedSec is an Ohio-based cybersecurity advisory firm recognized as a Forrester Wave Leader in Q2 2024 for cybersecurity consulting and CREST-accredited. Founded by prominent security practitioners, TrustedSec is known for its attacker-style thinking, deep technical expertise, and senior-consultant-led engagements. Their cloud penetration testing practice is highly customized, and their reports are notable for actionable prioritization and board-ready clarity.
Key Features & Services
- Manual cloud penetration testing across AWS, Azure, and GCP
- IAM analysis, cloud network segmentation review, and serverless security testing
- Red team engagements with cloud-specific kill chain scenarios
- Cloud incident response and forensics
- Security hardening and remediation advisory following cloud review
- Compliance-aligned assessments mapping to HIPAA, PCI DSS, ISO 27001, NIST, and CMMC
- Custom security program design for organizations building cloud security from the ground up
Pros
- Forrester Wave Leader Q2 2024 recognition provides strong independent analyst validation
- White-glove, senior-led engagements
- Deep compliance expertise means findings map naturally to audit control objectives
- Highly customized methodology that adapts to unusual or complex cloud architectures
- Findings are prioritized, contextualized, and written for both engineers and executives
Cons
- Premium pricing: among the higher price points for manual cloud reviews in North America
- Not a PTaaS or continuous model, engagement-based only
- A smaller team than NetSPI means capacity can be limited during peak periods
Pricing
Engagement-based, time-and-materials, or fixed-scope, depending on the project. Premium price point.
Best Suited For
Organizations that value a personalized, expert-led cloud security assessment and are willing to pay a premium for senior tester quality, deep customization, and compliance-grade reporting.
4. Bishop Fox
Bishop Fox is a Tempe, Arizona-based offensive security firm with a long-standing reputation for cutting-edge research and highly technical cloud penetration testing. Their consulting team regularly publishes original vulnerability research, discovers novel cloud attack chains, and contributes tooling to the security community. Bishop Fox's cloud security engagements go beyond configuration review: they simulate realistic multi-step cloud attacks, identify chained vulnerabilities that automated tools cannot detect, and provide deep strategic advice on architecture hardening. Their continuous security platform, Cosmos, provides clients with ongoing attack-surface visibility between point-in-time assessments.
Key Features & Services
- Advanced manual cloud penetration testing across AWS, Azure, and GCP
- Complex IAM analysis, including cross-account role chaining and privilege escalation mapping
- Container, Kubernetes, and serverless security assessments
- Red team engagements with cloud-specific multi-phase attack scenarios
- Cosmos continuous security platform for ongoing attack surface management between engagements
- Original cloud vulnerability research and custom exploit development
Pros
- Research-driven methodology means testers actively look for novel attack paths, not just known checks
- The Cosmos platform provides rare continuous visibility
- Strong publication record (CVEs, conference talks, open-source tools) signals genuine cloud expertise
- Well-suited for organizations with complex, custom cloud architectures that generic methodologies miss
Cons
- Premium pricing—positioned at the high end of the market
- A research-first culture may mean longer engagement timelines for deeply complex environments
- The Cosmos platform adds a subscription cost on top of assessment fees for clients wanting continuous monitoring
- Less emphasis on compliance-first framing compared to TrustedSec or Coalfire
Pricing
Engagement-based, with an optional Cosmos subscription for continuous coverage. Premium pricing tier.
Best Suited For
Organizations with complex, custom cloud environments that need a highly technical, research-driven assessment. Particularly those that have already completed basic cloud reviews and want to pressure-test sophisticated attack scenarios.
5. Rhino Security Labs
Rhino Security Labs created Pacu, the open-source AWS exploitation framework that is now part of Kali Linux and used by penetration testers industry-wide, as well as CloudGoat, the vulnerable-by-design AWS environment used for security training. This research pedigree is demonstrated by a library of original cloud attack techniques, IAM privilege escalation research, and GCP-specific vulnerability work that the broader security community relies on. Their engagements are manual, deep-dive, and informed by attacker research that few firms can match—a trusted security advisor to the Fortune 500.
Key Features & Services
- Manual AWS, GCP, and Azure cloud security assessments
- IAM privilege escalation path analysis
- Serverless function exploitation and assessment (Lambda, GCP Cloud Functions)
- S3 / cloud storage misconfiguration and access control review
- Container and Kubernetes security testing
- Custom cloud attack tool development and deployment for complex environments
- Web application and API security testing (often bundled with cloud review)
- Original cloud vulnerability research and responsible disclosure program
Pros
- Manual-only engagements with no outsourcing
- Deep IAM and privilege escalation expertise, including novel attack chains not covered by standard methodology
- Strong Fortune 500 and high-tech startup client base signals credibility across company sizes
- An active research culture means methodologies are continuously updated with new attack techniques
Cons
- Smaller boutique team (11–50 employees) means capacity is limited—lead times can be long
- Cloud-specialist focus means less breadth for clients needing bundled application and network testing
- Less compliance framework emphasis than firms like Coalfire or TrustedSec
Pricing
Custom-quoted, project-based engagements.
Best Suited For
Technology companies, high-growth SaaS firms, and Fortune 500 organizations are seeking the most comprehensive manual cloud assessment, especially for AWS-heavy environments, where IAM complexity and novel attack paths are the primary concerns.
6. Packetlabs
Packetlabs is a Toronto-based, CREST-accredited, and SOC 2 Type II-attested penetration testing firm. Founded over 12 years ago, Packetlabs has built its entire brand around a 95% manual testing methodology with a strict no-outsourcing guarantee. Their cloud penetration testing practice explicitly targets the SaaS environment: multi-tenant architectures, CI/CD pipeline security, cloud-native APIs, and the compliance requirements (SOC 2, ISO 27001, PCI DSS, PIPEDA) that enterprise SaaS buyers demand. Notably, Packetlabs offers both a Cloud Penetration Test (attacker-simulation) and a Cloud Penetration Review (configuration audit) as distinct services, or combined as an enhanced bundle.
Key Features & Service
- Manual cloud penetration testing across AWS, Azure, and GCP (95% manual, no outsourcing)
- Cloud Penetration Review
- Enhanced Cloud Security Bundle (penetration test + configuration review combined)
- IAM analysis, privilege escalation paths, and container security review
- CI/CD pipeline security testing for SaaS DevOps environments
- Ransomware penetration testing with cloud-specific attack scenarios
- Compliance-mapped findings for SOC 2, ISO 27001, PCI DSS, NIST SP800-115, PIPEDA, NIS2
- Packetlabs Portal: client-facing platform for tracking findings, requesting retests, and monitoring progress
- Complimentary retest of all critical and high findings included in the base scope
Pros
- 95% manual testing with no outsourcing guarantee
- CREST accreditation + SOC 2 Type II attestation provides dual third-party quality validation
- Purpose-built for SaaS and technology companies
- Zero false positives guarantee
- Canadian-domiciled firm with Canadian data residency
Cons
- Smaller team size means capacity can be constrained during peak demand periods
- Less international reach than NetSPI or NCC Group for clients with global cloud deployments
- Packetlabs Portal, while useful, is less mature than NetSPI's PTaaS platform for large-scale programs
Pricing
Project-based fixed-scope pricing. Engagements typically range from $30,000–$100,000 depending on the environment complexity.
Best Suited For
SaaS companies and technology organizations across North America that want a rigorous manual cloud review with no outsourcing, strong compliance mapping, and a credible peer-level alternative to US-based specialist firms.
7. NCC Group

NCC Group is a UK-headquartered global cybersecurity firm. As one of the largest pure-play cybersecurity consultancies in the world, NCC Group brings encyclopedic technical depth to cloud security assessments, with vendor-agnostic expertise across AWS, Azure, and GCP. They regularly publish original research, contribute to CVE disclosures, and serve large enterprises and government entities in regulated industries. NCC Group is not the right fit for every buyer because its engagements are typically premium-priced and geared toward organizations with complex, high-stakes cloud environments. For those who qualify, they deliver rigorous, strategically oriented assessments that go far beyond a checklist.
Key Features & Services
- Comprehensive cloud penetration testing across AWS, Azure, and GCP
- Cloud configuration audit and security posture assessment
- Complex IAM analysis and cloud identity security review
- Container and Kubernetes security testing
- Supply chain and CI/CD pipeline security assessments
- Cloud security architecture advisory and secure design review
- Compliance mapping for FedRAMP, HIPAA, PCI DSS, ISO 27001, SOC 2, and government frameworks
- Incident response and cloud forensics capability
Pros
- Global scale provides access to specialized expertise that smaller firms cannot offer
- Vendor-agnostic technical depth across all three major cloud providers
- Strong publication record and original research signal genuine cloud attack knowledge
- Well-suited for organizations with complex, multi-cloud environments spanning multiple geographies
- Strategic advisory capability beyond technical findings
Cons
- Premium pricing is typically geared toward large enterprises and government clients
- Fixed-scope, traditional engagement model, and not a continuous or PTaaS offering
- Longer engagement timelines due to the depth of analysis
- Less brand familiarity in the North American SaaS startup ecosystem
Pricing
Traditional fixed-scope engagements. Premium pricing tier.
Best Suited For
Large enterprises, government entities, and organizations with highly sensitive or regulated cloud environments are seeking a comprehensive expert-led assessment and strategic security advisory
8. Coalfire
Coalfire is a services firm that occupies a unique position in the cloud security market: it is both a penetration testing firm and an accredited Third-Party Assessment Organization (3PAO) authorized to conduct official FedRAMP assessments. With over 200 cloud services assessed for FedRAMP authorization, Coalfire's testers possess encyclopedic knowledge of what passes federal scrutiny, making them the dominant choice for cloud service providers pursuing government contracts. Beyond FedRAMP, Coalfire's cloud security practice extends to SOC 2, PCI DSS, HIPAA, and CMMC, offering compliance-first security assessments where every finding is contextualized for auditor consumption.
Key Features & Services
- FedRAMP penetration testing and pre-assessment (3PAO accredited)
- Cloud security assessment aligned to NIST SP 800-53 CA-8 requirements
- PCI DSS, SOC 2, HIPAA, and CMMC compliance-aligned cloud reviews
- Cloud configuration audit and security posture assessment
- IAM and identity security review with compliance mapping
- Cloud architecture advisory for organizations building toward FedRAMP authorization
- Managed compliance and continuous monitoring services post-authorization
Pros
- Only firm on this list with 3PAO accreditation, making them uniquely qualified for FedRAMP cloud reviews
- 200+ FedRAMP assessments provide unmatched institutional knowledge of federal cloud requirements
- Compliance-first methodology means every finding is formatted for auditor review
- Strong breadth across all major compliance frameworks relevant to regulated industries
- North American HQ with a deep federal and regulated-industry client base
Cons
- Compliance specialists first, penetration testers second
- Premium pricing reflecting specialized compliance expertise
- Less relevant for SaaS companies that do not have FedRAMP or federal compliance requirements
- Engagement model optimized for compliance outcomes rather than attacker-centric threat modeling
Pricing
Compliance-driven, fixed-scope engagement pricing. Premium tier reflecting 3PAO accreditation and specialized federal expertise.
Best Suited For
Cloud service providers who are pursuing FedRAMP authorization, and organizations in highly regulated industries (healthcare, financial services, federal contractors), where cloud security assessments must satisfy strict auditor and regulatory requirements.
9. GuidePoint Security

GuidePoint Security is one of the larger pure-play cybersecurity advisory and professional services firms in North America, headquartered in Herndon, Virginia. Their portfolio spans managed detection and response, GRC, application security, and cloud security. Their cloud security practice covers all three major cloud providers, operates at the AWS Advanced Partner tier, and serves mid-market through large enterprise clients. GuidePoint's retainer and managed services models are particularly well-suited to organizations that need ongoing cloud security advisory beyond a single point-in-time assessment.
Key Features & Services
- Cloud Security Posture Management (CSPM) consulting and tool deployment
- Cloud architecture security review and design advisory
- IAM hardening and identity security review across AWS, Azure, and GCP
- Container and Kubernetes security assessment
- Cloud incident response, forensics, and threat hunting
- Compliance and regulatory mapping (FedRAMP, HIPAA, PCI DSS, CMMC, SOC 2)
- Managed cloud security monitoring and detection services
- Security technology selection and integration advisory
Pros
- A broad multi-domain portfolio enables single-vendor engagements across cloud, application, and network security
- Strong technology partnership ecosystem
- Retainer and managed service models available for clients needing ongoing advisory, not just point-in-time reviews
- Wide geographic coverage across North America with a large team capacity
- Well-suited for mid-market clients that lack internal security staff and need advisory breadth
Cons
- Breadth may mean less SaaS-specific depth than cloud specialists like Rhino Security Labs or Software Secured
- Higher price point for enterprise-scale engagements may be out of scope for early-stage SaaS
- Assignment quality can vary on larger projects where senior vs. junior staffing is less predictable
- Cloud security is one of many service lines
Pricing
Retainer and time-and-materials based.
Best Suited For
Mid-market to enterprise organizations requiring a broad cybersecurity advisory partner with cloud security as one component of a larger engagement, particularly those that want a single firm to address cloud, GRC, and managed security simultaneously.
10. LevelBlue
LevelBlue has a cloud security engagement benefit from this continuous attacker-perspective research and is complemented by a PTaaS platform (Insight Cloud) that allows clients to track findings, compliance status, and remediation progress in a single dashboard. LevelBlue serves enterprise clients across financial services, retail, healthcare, and technology sectors with 1,000+ test engagements annually.
Key Features & Services
- Manual cloud penetration testing across AWS, Azure, and GCP
- Internal, external, and cloud infrastructure penetration testing
- Red and blue team exercises with cloud-specific attack scenarios
- Adversary emulation using threat intelligence and proprietary attack simulation
- Compliance-mapped assessments for PCI DSS, HIPAA, SOC 2, and ISO 27001
- Managed security services and MDR (detection and response) integrated with cloud environments
Pros
- Insight Cloud platform enables continuous compliance tracking and remediation management between assessments
- 1,000+ test engagements annually provide meaningful scale and methodology refinement
- Strong financial services and retail sector expertise with compliance-grade reporting
Cons
- Large organization size means engagement quality can vary depending on team assignment
- A platform-first delivery model may feel less boutique compared to TrustedSec or Bishop Fox
- Less specialized in SaaS-specific cloud architectures compared to focused specialists
- Pricing and engagement minimums calibrated for enterprise buyers rather than growth-stage SaaS
Pricing
Subscription (PTaaS/Insight Cloud) and project-based engagement models—enterprise pricing tier.
Best Suited For
Enterprise organizations in financial services, retail, and healthcare that want a research-backed cloud security assessment with a continuous compliance tracking platform and the option to roll into managed security services.
Why Software Secured Does the Best Job at Auditing Cloud Security
By the time organizations begin evaluating secure cloud review providers, they typically already understand the stakes: misconfigured identity systems, exposed secrets, and overly permissive infrastructure roles are now among the most common causes of major SaaS security incidents. What matters at this stage is not simply choosing a vendor but choosing one whose methodology reflects how real attackers actually move through modern cloud environments.
The Manual-First Difference
At Software Secured, automation is used to assist analysts, not replace them. Every secure cloud review is driven by manual analysis of identity permissions, infrastructure relationships, and service interactions.
For example, a high-severity cloud privilege escalation chain might not appear dangerous when viewed as individual IAM policies. A developer role may have permission to modify a CI/CD pipeline configuration. That pipeline may be able to assume a production deployment role. Individually, neither permission appears critical. But when traced together, they can allow a compromised developer account to deploy malicious infrastructure into production.
This type of multi-step escalation path is extremely difficult for automated tools to detect because it requires contextual reasoning across multiple identities, services, and trust relationships. Manual analysis makes these chains visible.
Built for SaaS Environments
Software Secured works almost exclusively with SaaS companies, which means its methodology is tuned to the security patterns that recur across cloud-native software platforms. Since a security report has little value if the findings are never remediated, they structure engagements to maximize remediation success:
- Findings are written primarily for the engineers responsible for fixing them, with clear reproduction steps and remediation guidance.
- Every engagement includes a live walkthrough session where testers explain attack paths directly to the development team.
- Critical and high-severity findings are retested at no additional cost to verify remediation.
- Executive summaries are formatted to be shared directly with boards, investors, or enterprise procurement teams.
Transparent, Fixed-Scope Pricing
Cloud security reviews should not come with unpredictable consulting invoices. Software Secured defines the scope of each engagement upfront, based on the cloud environment's size, complexity, and testing objectives, and prices the work as a fixed-fee project. This allows engineering and security leaders to plan budgets confidently without the risk of open-ended time-and-materials billing.
FAQ
What is a cloud security assessment?
A cloud security assessment is a manual review of your cloud environment, covering identity and access management configuration, storage permissions, network segmentation, CI/CD pipeline security, logging and monitoring coverage, and infrastructure-as-code security. It identifies misconfigurations and access control gaps that automated tools flag but cannot fully validate in the context of your specific architecture.
What cloud environments and providers do assessments cover?
Cloud security assessments cover major providers including AWS, Azure, and Google Cloud, as well as multi-cloud and hybrid environments. Key areas include IAM policy review and privilege escalation paths, S3 or blob storage permissions, VPC and network security group configuration, Kubernetes and container security, serverless function permissions, and secrets management in CI/CD pipelines.
What are the most common cloud security misconfigurations?
The most frequently exploited cloud misconfigurations include overly permissive IAM roles and policies, publicly exposed storage buckets containing sensitive data, unrestricted security groups allowing unintended network access, hardcoded credentials in CI/CD pipelines or code repositories, missing logging and monitoring coverage leaving attackers undetected, and insecure cross-account trust relationships enabling lateral movement between environments.
How often should SaaS companies review their cloud security?
Cloud environments change constantly; when new services are deployed, IAM policies are modified, and infrastructure-as-code updates introduce new configurations daily. SaaS companies should conduct a formal cloud security assessment at least annually and after major architectural changes. Teams using infrastructure-as-code should also integrate automated policy scanning into their CI/CD pipeline to catch misconfigurations before they reach production.
Choosing the Right Secure Cloud Review Partner
Cloud security reviews have become a critical step for SaaS companies operating in increasingly complex multi-cloud environments. As the examples throughout this guide demonstrate, many high-profile cloud incidents originate not from a single vulnerability but from chains of small misconfigurations across identity systems, CI/CD pipelines, and infrastructure services. Identifying these attack paths requires more than automated scanning. It requires experienced analysts who understand how modern SaaS architectures are actually built and operated.
The vendors listed in this guide all bring valuable capabilities to the table. Large enterprise consultancies offer scale and compliance expertise, while specialist firms provide deeper offensive testing and research-driven methodologies. The right choice ultimately depends on the organization’s stage, architecture complexity, and security maturity.
For SaaS companies seeking a rigorous, manual-first cloud security review aligned with both engineering realities and compliance expectations, Software Secured provides a methodology specifically designed for the challenges of modern cloud-native software platforms.
Organizations considering a secure cloud review can start by evaluating their current cloud architecture, defining the scope of environments to assess, and selecting a provider whose methodology aligns with how attackers actually operate in cloud environments today.




.avif)
