Reentrancy, Flash Loans, and the Real Threat Model for Web3 Security
This article explores how attackers exploit DeFi protocols using economic attack paths, not just code-level bugs. Learn how to evaluate smart contract security in real-world conditions.
When engineering teams first move into Web3, they often assume smart contract security is simply a harder version of application security. Learn Solidity, adopt new tooling, and apply familiar practices like code review, dependency scanning, and penetration testing.
In reality, the security model is different. Many of the largest DeFi exploits do not stem from classic software vulnerabilities such as injection flaws or authentication failures. Instead, they arise from economic attack paths: sequences of transactions that manipulate protocol mechanics to extract value.
Understanding Web3 security requires thinking not only like a software engineer, but also like a trader, arbitrageur, or market manipulator. The attack surface is not just the code itself; it is the economic system that the code creates.
Why Most Web3 Attacks Target Smart Contracts
It’s important to distinguish between the blockchain itself and the applications built on top of it. Public blockchains such as Ethereum are heavily studied and extremely difficult to attack directly. Breaking consensus or corrupting the ledger typically requires enormous computational resources or control over a large portion of the network.
As a result, attackers rarely target the base layer, and instead, they target smart contracts.
Smart contracts are programs that run on-chain and control real assets. Lending protocols, decentralized exchanges, derivatives markets, and DAO governance systems all rely on contract logic to manage funds automatically.
If that logic contains flaws or if the protocol design can be economically manipulated, attackers can extract funds instantly.
Unlike traditional financial systems, there is typically:
- No administrator to reverse transactions
- No centralized fraud team
- No ability to roll back mistakes
Once a transaction executes, the funds are gone.
This is why smart contract vulnerabilities have become the dominant failure mode in Web3 security.
The Missing Mental Model: Economic Attacks
Traditional application security focuses on access control and system integrity.
Typical questions include:
- Who should be allowed to perform this action?
- Can an attacker bypass authentication?
- Is user input validated correctly?
Smart contract security introduces a different question:
If someone can interact with this system freely and has strong financial incentives, what sequence of actions could extract value?
This is an economic adversary model.
Attackers are not trying to break the system in obvious ways. Instead, they look for ways to legally interact with the protocol while producing unintended outcomes.
A protocol may behave exactly as coded and still lose money.
Flash Loans: The Capital Amplifier
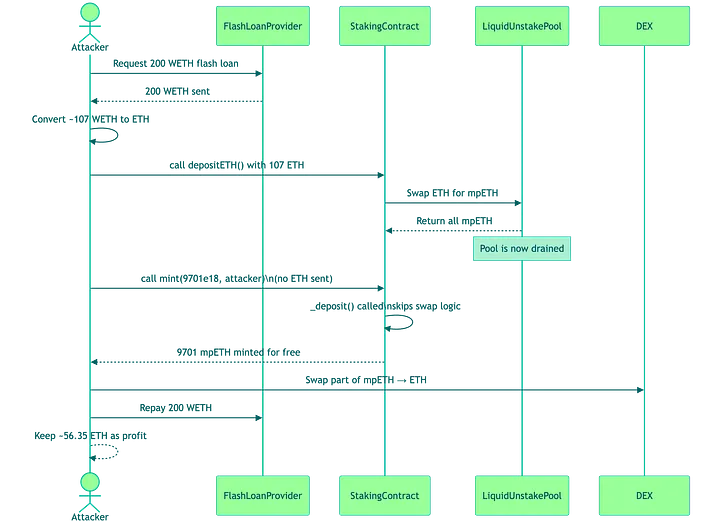
One mechanism that makes these attacks possible is the flash loan.
A flash loan allows users to borrow large amounts of cryptocurrency without collateral, provided the loan is repaid within the same transaction.
If the loan cannot be repaid, the entire transaction automatically reverts.
Flash loans themselves are not vulnerabilities. They are legitimate DeFi tools used for arbitrage, collateral swaps, and liquidity management. However, they dramatically increase the scale of potential attacks.
With a flash loan, an attacker can temporarily access hundreds of millions of dollars in liquidity, manipulate markets or protocol mechanics, extract value, and repay the loan, all within a single block. Several high-profile DeFi exploits have relied on this mechanism, including attacks on protocols like bZx, Mango Markets, and Euler Finance.
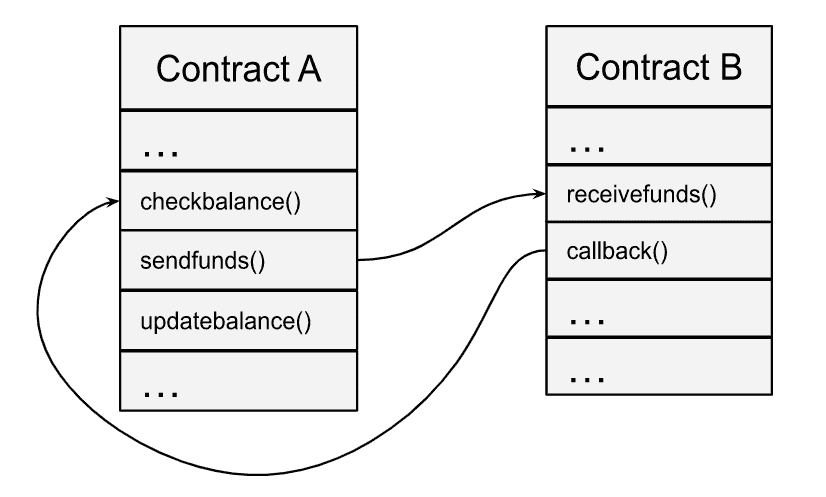
Reentrancy: The Classic Smart Contract Vulnerability
One of the most well-known vulnerabilities in Web3 security is reentrancy. Reentrancy occurs when a contract calls an external address before updating its internal state. If the external contract is malicious, it can call back into the original function before the state change occurs. This allows the attacker to repeat the operation multiple times.
In practical terms, the attacker can withdraw funds repeatedly using the same balance. The most famous example is the 2016 DAO exploit.
The DAO was an early decentralized investment fund built on Ethereum. Investors deposited ETH into the contract and received voting tokens that controlled how the capital would be allocated. At its peak, the DAO held roughly $150 million worth of ETH.
The contract’s withdrawal logic contained a flaw: it transferred funds before updating the user’s balance. An attacker exploited this by repeatedly calling the withdrawal function through a malicious contract. Each recursive call executed before the balance update occurred.
The exploit drained 3.6 million ETH, roughly one-third of the DAO’s total funds. The incident ultimately led to the controversial Ethereum hard fork.
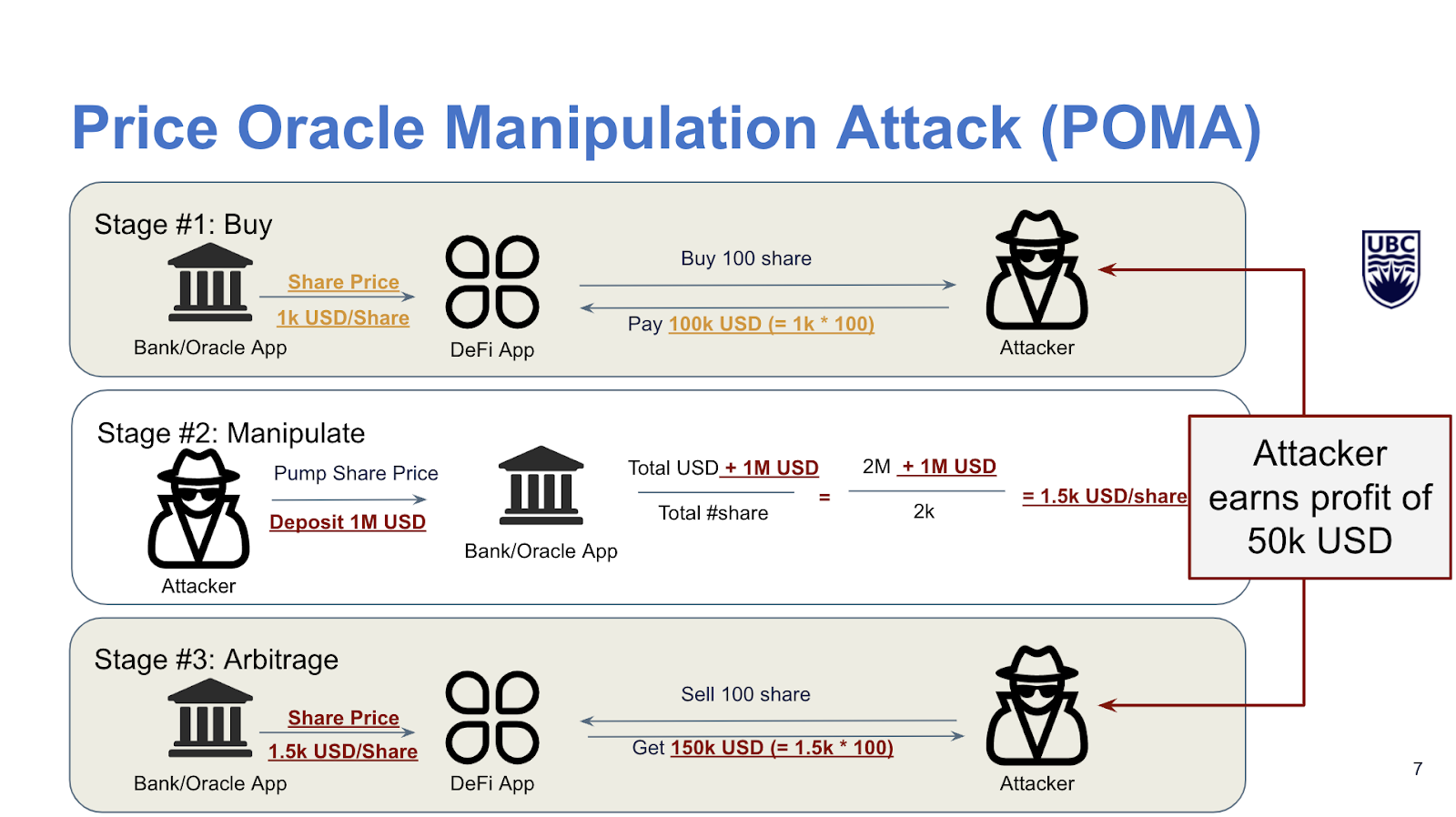
Oracle Manipulation: When Prices Become Attack Surfaces
Many DeFi protocols rely on oracles to obtain price information because blockchains cannot access external data directly. Oracles provide price feeds for assets like ETH, BTC, or stablecoins. If a protocol relies on a weak oracle design, attackers may be able to manipulate it.
For example:
A lending protocol might accept collateral based on a token’s market price. If that price comes from a low-liquidity on-chain pool, an attacker could temporarily move the market using borrowed funds.
The manipulated price is then used to:
- Overvalue collateral
- Borrow excess assets
- Extract funds from the protocol
Once the transaction finishes, the price returns to normal, but the attacker has already captured the profit. This type of exploit has appeared repeatedly across DeFi ecosystems.
Composability and the Expanding Attack Surface
Another unique aspect of Web3 security is protocol composability. Smart contracts rarely operate in isolation. DeFi protocols frequently interact with:
- Liquidity pools
- Lending markets
- Token bridges
- Derivatives protocols
These integrations create powerful financial ecosystems, but they also introduce complex dependencies. Many exploits occur not because a single contract is broken, but because multiple protocols interact in unexpected ways.
Attackers study these interactions closely. They may chain together several legitimate operations across multiple protocols to produce outcomes the designers never anticipated.
What Good Smart Contract Security Looks Like
Evaluating Web3 security requires looking beyond a simple audit checklist. Automated tools and analysis techniques remain valuable. These include:
- Static analysis of Solidity code
- Fuzz testing of contract logic
- Dynamic testing on local networks
- Manual code review
- Threat modeling
Frameworks like the OWASP Smart Contract Top 10 help categorize known vulnerabilities. However, the most dangerous attacks often arise from economic design flaws, not coding errors. Because of this, high-quality smart contract security reviews combine:
- Code-level vulnerability analysis
- Protocol design analysis
- Economic attack modeling
Experienced auditors will explore scenarios such as:
- Flash loan amplification
- Liquidity manipulation
- Oracle dependency risks
- Cross-protocol interactions
- Governance manipulation
The Role of AI in Smart Contract Security
AI tools are becoming increasingly useful in Web3 security workflows. They are particularly effective at identifying known vulnerability patterns such as:
- Reentrancy risks
- Integer overflows
- Unsafe external calls
- Access control mistakes
AI can also quickly analyze large volumes of smart contract code, making it easier to detect patterns across multiple projects. However, AI still struggles with novel economic exploits.
Many major DeFi attacks involve creative combinations of:
- Liquidity dynamics
- Protocol dependencies
- Transaction ordering
- Governance mechanisms
These scenarios require contextual reasoning about how value flows through the system. Human expertise remains critical.
Rethinking the Web3 Threat Model
Smart contract security is not simply application security with a different programming language.
It combines three domains:
- Software engineering
- Financial market mechanics
- Adversarial economic behavior
For engineering teams building Web3 infrastructure, this means security must be considered in protocol design, not just in code review. For security leaders, it means evaluating more than whether a project has completed an audit.
The more useful questions include:
- What economic attack scenarios were modeled?
- Does the audit consider flash loan amplification?
- Are oracle dependencies robust?
- How does the protocol behave under extreme liquidity conditions?
In Web3 systems, the code is public, the incentives are financial, and exploits are irreversible. That combination creates one of the most challenging security environments modern engineering teams have ever faced.
Web3 security ultimately sits at the intersection of software engineering and financial system design. Code may define the rules, but incentives determine how those rules are tested.
As DeFi ecosystems grow more interconnected, the most dangerous exploits will continue to come from unexpected combinations of protocol mechanics rather than simple coding errors. Teams that understand this shift and design their systems with economic adversaries in mind will be far better positioned to build resilient on-chain infrastructure.
The attack patterns behind reentrancy and flash loan exploits don't stay in Web3, many of the same logic flaws show up in traditional web applications. If your team is building anything that handles financial transactions or user funds, a web application penetration test can surface these issues before an attacker does.
Web3 Security FAQ
What is the most common smart contract vulnerability?
Reentrancy is one of the most well-known vulnerabilities. It occurs when a smart contract makes an external call before updating its internal state, allowing attackers to repeat the operation multiple times.
Are flash loans inherently dangerous?
No. Flash loans are legitimate DeFi tools used for arbitrage and liquidity management. They become dangerous when protocols fail to account for how attackers could use temporary liquidity to manipulate markets or protocol mechanics.
Why are smart contract exploits irreversible?
Blockchain transactions are typically immutable. Once a transaction is confirmed, there is no central authority capable of reversing it.
I



.avif)
