Top 10 Social Engineering Testing Companies (Red Team & Phishing) in 2026
This guide breaks down the top 10 social engineering testing providers for 2026, from boutique red team specialists to enterprise-grade firms like Mandiant and Bishop Fox. Whether you're building a human-risk program from scratch or maturing an existing one, this article helps you understand the difference between awareness platforms and adversarial testing and how to choose the right partner for your organization's needs.
Social engineering is one of the most persistent and expensive threats facing organizations today, and it keeps getting harder to defend against. Attackers no longer need to crack your firewall or exploit a zero-day vulnerability. They just need one employee to click a link, answer a call, or hold a door open. Once that happens, the damage can be done in seconds.
If you are responsible for your organization's security posture, you already know that technical controls alone are not enough. The question is not whether to test your human defenses. It is who should be doing it and how.
This guide breaks down the top social engineering service providers, explains what actually separates awareness platforms from adversarial red team testing, and gives you a practical framework for building a defensible program, whether you are starting from scratch or maturing an existing one.
Why Social Engineering Remains a Leadership-Level Risk
Social engineering is best understood as an attack family that targets people and processes rather than software flaws. The National Institute of Standards and Technology (NIST) characterizes it as any attempt to trick an individual into revealing information or taking an action that can be used to breach or adversely impact a system. Common variants include phishing, pretexting, impersonation, baiting, quid pro quo, thread-jacking, social media exploitation, and tailgating.
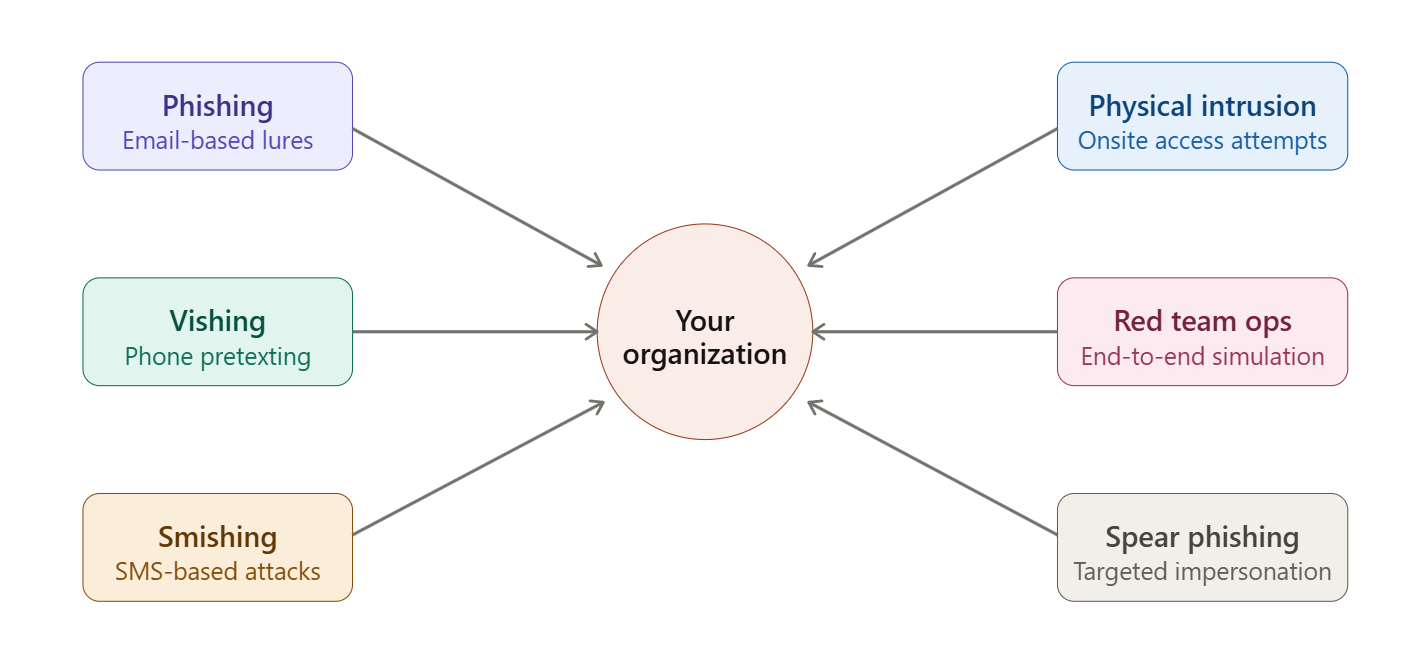
That definition matters operationally because it points security leaders toward a consistent conclusion: your organization's attack surface includes identity workflows, approval processes, customer-facing touchpoints, and physical access routines. Anywhere trust can be exploited is fair game.
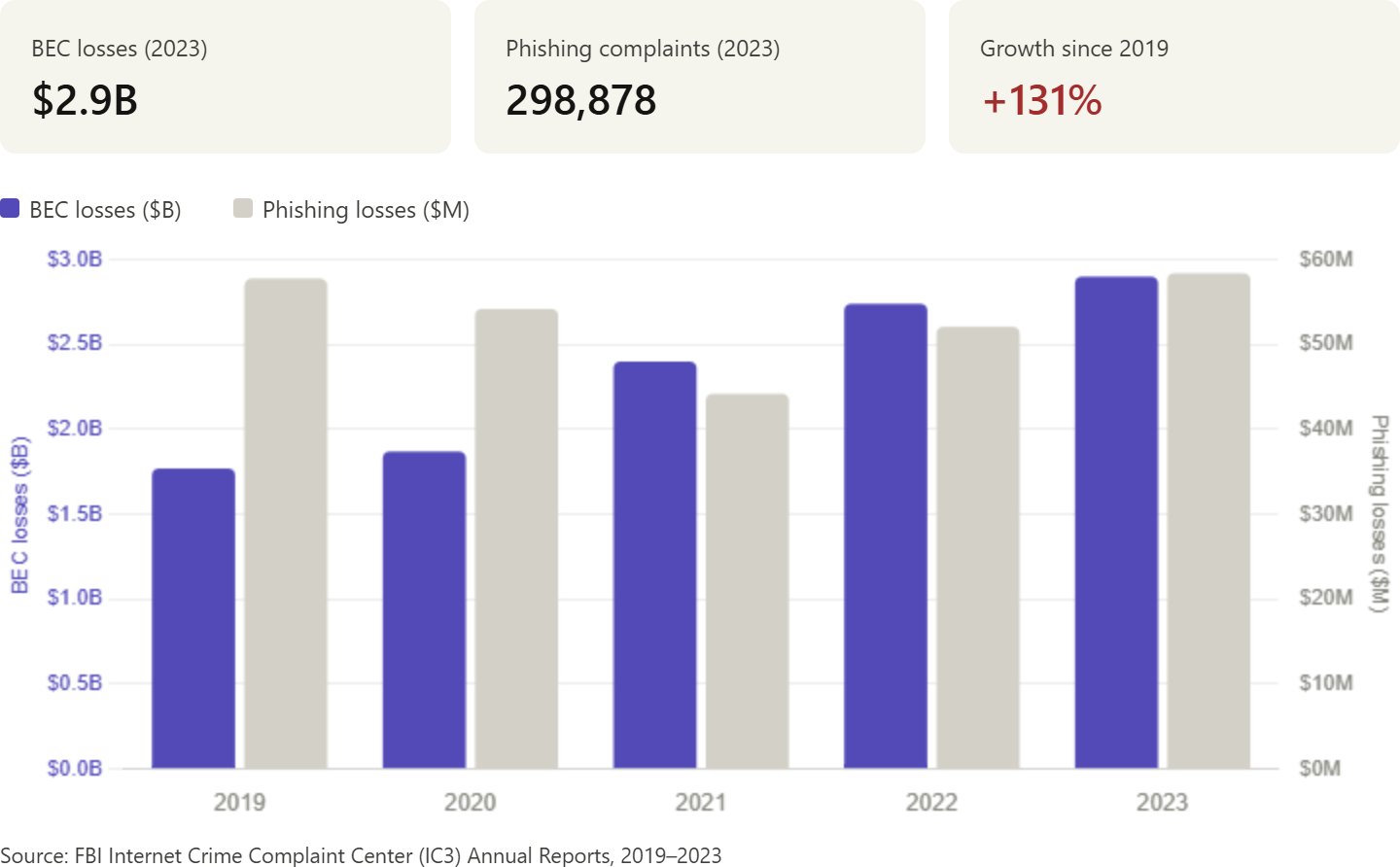
Verizon's breach analysis consistently finds that a significant portion of confirmed breaches involve a human element, and the FBI's Internet Crime Complaint Center (IC3) lists phishing and spoofing as the highest-volume complaint categories by count, with Business Email Compromise (BEC) driving multi-billion-dollar losses annually. Security awareness exercise data suggest the median time between opening a phishing email and falling for it is under a minute. Once a lure reaches an employee, your window to stop the first mistake from turning into unauthorized access is extremely small.
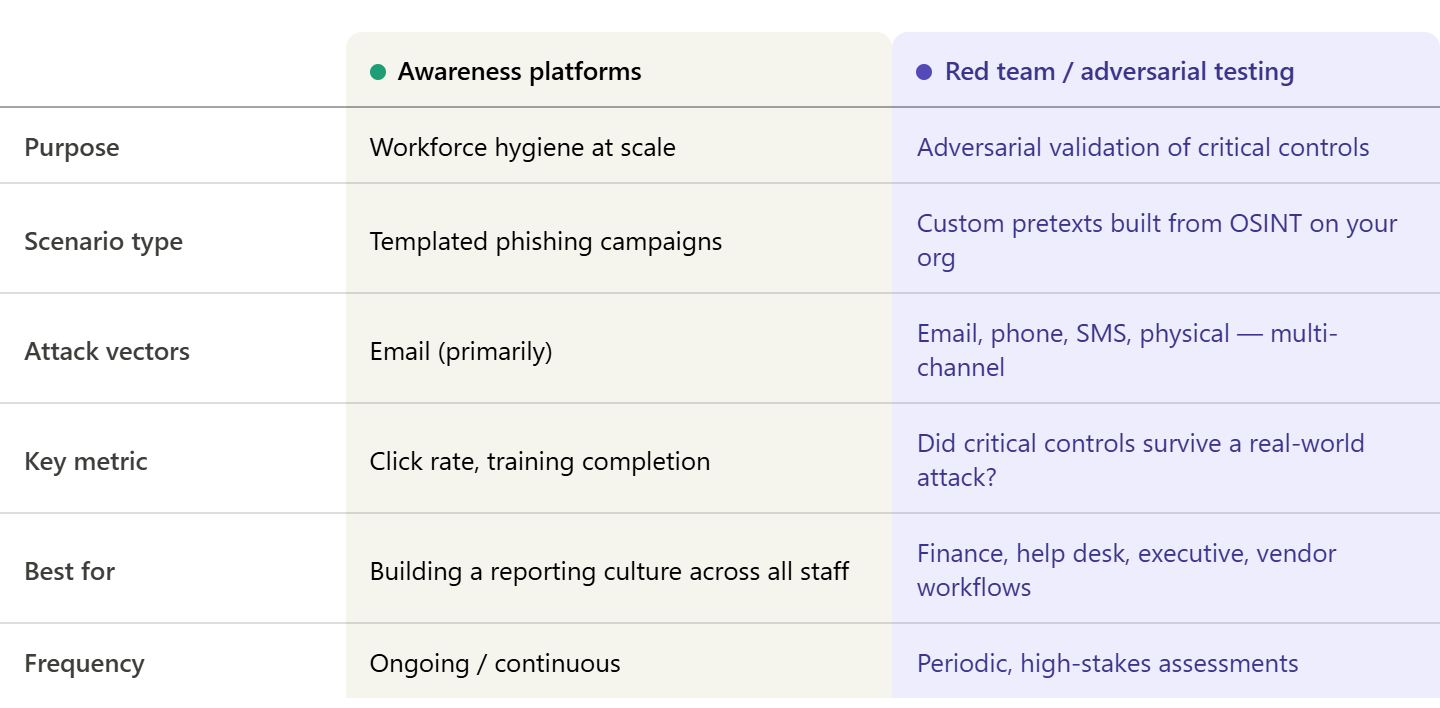
Awareness Platforms vs. Adversarial/Red Team Social Engineering
One of the most common mistakes organizations make when building a social engineering defense program is treating all providers as interchangeable. They are not. There are two fundamentally different categories of services on the market, and choosing the wrong one for your highest-risk gaps is expensive in more ways than one.
Selecting the Right Partner in a Crowded Provider Ecosystem
The social engineering provider market is crowded because it spans multiple service types that appear similar in procurement documents yet yield different outcomes. Before evaluating specific vendors, clarify which category your highest-risk gaps fall into.
Across all provider types, push due diligence beyond feature checklists and require evidence in five areas.
Methodology transparency. Ask providers to map their approach to recognized guidance, such as NIST's planning-to-reporting phases for penetration testing or CREST's preparation, testing, and follow-up program framing. Providers who cannot articulate how scoping, safety, and reporting work are a procurement risk.
Ethics, safety, and workforce trust protections. Require a documented approach that treats testing as a means of improving systems, not as a way to punish individuals. Poorly designed simulated phishing campaigns have been documented to cause unnecessary employee stress and erode trust. Good providers know this and build guardrails into their methodology.
Data handling and privacy. Human-risk testing generates sensitive workforce data. Require explicit terms for retention, access, and deletion before signing anything.
Outcome quality. Reports should be decision-ready: which controls failed, which process steps enabled the failure, and which mitigations reduce both the likelihood and the blast radius. Click rates alone are not enough.
Measurement integrity. Demand metrics that reflect meaningful risk reduction, such as workflow verification compliance, reporting speed, repeat-failure rates, and incident response quality, rather than whether employees clicked or did not click on a simulated phishing email.
Why Trust Us?
We have spent over a decade embedded in the penetration testing and offensive security space, working with SaaS companies, scaling tech teams, and enterprise security programs. That work gives us a ground-level view of what separates a strong social engineering assessment from a compliance checkbox exercise.
We evaluate vendors based on methodology depth, scenario realism, report quality, and what actually happens after the assessment is delivered. A social engineering test that does not change anything is not worth the invoice.
We also know that the security community is smaller than it looks, and the gap between a vendor's marketing and their actual fieldwork can be significant. Our rankings are informed by technical rigor, real-world engagement experience, and direct feedback from security practitioners who have worked with these providers.
Top 10 Social Engineering Service Providers
The vendors below represent the strongest options available across the spectrum of social engineering services. To help IT leaders make an informed purchasing decision, each profile includes a summary, key service details, notable pros and cons, and the types of organizations best suited to each provider.
1. Software Secured
Headquarters: Canada, Founded: 201,0 Best for: B2B SaaS companies and high-growth tech firms needing manual, exploit-driven testing with compliance-ready outcomes
Overview
Software Secured is a manual penetration testing company with a specific focus on SaaS organizations. Their social engineering testing is integrated within broader web application, network, and red team engagements, allowing IT leaders to see how human-layer compromise connects to technical attack paths. Pretexts are custom-built based on reconnaissance of your actual environment.
Services offered: Phishing simulations, vishing, spear phishing, pretexting, social engineering integrated with web/API and network pentesting, red teaming, threat modeling, secure code review, PTaaS
Pros
- Custom pretexts built from active reconnaissance, not templates
- Social engineering is tied to the full technical attack chain, so findings show end-to-end impact
- Retesting included for up to six months post-report at no additional cost
- Reports mapped to SOC 2, ISO 27001, PCI DSS v4.0, HIPAA, and GDPR
- Purpose-built Portal with Jira, Slack, Vanta, and Drata integrations
- Transparent, fixed pricing with no mid-engagement scope creep
- Full-time senior Canadian pentesters with no crowdsourcing
Cons
- Primary focus is on SaaS and cloud-native organizations; less optimized for legacy on-premise environments.
- Not the right fit if you need standalone security awareness training at a workforce scale
- Physical social engineering (onsite intrusion) is available, but not a primary service focus.
Ideal for:
- SaaS companies under SOC 2, ISO 27001, or PCI pressure
- Tech companies are closing enterprise deals that require security evidence.
- IT and security teams that want social engineering findings connected to technical risk
2. Social-Engineer, LLC

Headquarters: United States, Founded: 2010, Best for: Organizations that want a specialist provider focused exclusively on the human attack surface
Overview
Social-Engineer, LLC is one of the few vendors in the market that treats social engineering as a primary discipline rather than a service line within a broader penetration testing portfolio. Social-Engineer, LLC has built its entire practice around the human attack surface, developing deep expertise in the psychology, methodology, and operational execution of social engineering engagements.
Services offered: Phishing, vishing (human-operated), smishing, physical social engineering, impersonation, OSINT, security awareness, and training
Pros
- Deep specialization in social engineering with no dilution across other cybersecurity services
- Human-operated vishing produces significantly more realistic outcomes than automated call campaigns.
- Strong OSINT capability built into every engagement
- Well-regarded training and educational resources for security teams
Cons
- Narrower service portfolio than full-scope pen testing firms; does not integrate with technical attack path testing
- Physical engagement logistics can add complexity and lead time for a multi-site organization.s
- Pricing is not publicly listed and can be higher than generalist providers for comparable scope.
Ideal for: Organizations whose highest-risk exposures involve phone-based pretexting, help desk impersonation, or executive-targeted social engineering; security teams that want a subject-matter specialist rather than a generalist firm.
3. Bulletproof
Headquarters: United Kingdom, Founded: 2001, Best for: Organizations seeking a managed security partner that integrates social engineering within a broader security services framework
Overview
Bulletproof is a managed security services provider with an offensive security practice that includes social engineering assessments. Their approach contextualizes social engineering findings within an organization's wider threat landscape, making them a practical choice for teams that want testing connected to ongoing security operations rather than delivered as a standalone exercise.
Services offered: Phishing campaigns, vishing, physical penetration testing, managed detection and response, vulnerability management, penetration testing
Pros
- Strong integration between offensive security testing and managed security services
- Reporting is oriented toward business risk, making findings accessible to non-technical stakeholders.
- A broad service portfolio makes it easier to manage multiple security workstreams with a single vendor.
- UK-based with a strong understanding of regulatory environments, including GDPR and FCA requirements
Cons
- Social engineering is one service line within a large managed services portfolio; it may not receive the same specialization depth as dedicated offensive security firms.
- Organizations based outside the UK or EU may find the primary compliance focus misaligned with their regional requirement.s
- Less suitable for organizations that want red team-grade adversary emulation integrated with technical compromise testing
Ideal for: UK and EU-based organizations looking for a long-term managed security partner; companies that want social engineering testing embedded within ongoing security operations rather than as a periodic engagement.
4. GuidePoint Security
Headquarters: United States (Herndon, Virginia) Founded: 2011 Best for: Organizations that need highly customized social engineering scenarios tied to specific workflows and business processes
Overview
GuidePoint Security takes a consultative approach to social engineering engagements. Rather than arriving with predefined scenarios, their team works closely with clients to understand the specific workflows, trust relationships, and business processes most likely to be targeted, and builds pretexts around those realities.
Services offered: Phishing campaigns, phone pretexting (vishing), onsite impersonation, physical penetration testing (lock picking, badge cloning, rogue devices), social engineering integrated with full-scope red team assessments
Pros
- Highly customized engagement design with strong client collaboration throughout scoping
- Physical security testing capabilities are notably comprehensive, including badge replication and rogue device placement.
- Social engineering integrates with broader red team exercises for full attack chain validation.
- Established US-based firm with a track record across multiple industries
Cons
- Engagement model tends toward longer scoping cycles, which may not suit organizations with a tight timeline.s
- Pricing is not publicly disclosed and scales with engagement complexity
- Less suitable for organizations that need rapid, high-frequency, lightweight phishing simulations rather than full scenario-based assessments
Ideal for: Mid-market to enterprise organizations with complex physical and digital attack surfaces; security teams that want social engineering tied to a full red team engagement rather than isolated testing.
5. Redbot Security
Headquarters: United States (Denver, Colorado). Founded: Listed as active; boutique firm. Best for: Organizations seeking a boutique, senior-led red team with strong specialization in multi-phased adversary emulation
Overview
Redbot Security operates as a specialist offensive security firm focused on manual penetration testing and red team services. Every engagement is led by senior-level, certified practitioners. Their social engineering capabilities are integrated into Red Team Security Exercises. The firm emphasizes continuous improvement and provides detailed remediation guidance designed to help clients improve measurably between engagements.
Services offered: Multi-phased red team exercises, social engineering (phishing, vishing, pretexting), network and infrastructure penetration testing, IT and OT/ICS testing, cloud security assessments
Pros
- All engagements led by senior engineers, no use of junior testers on active assessments
- Multi-phase approach connects social engineering to lateral movement and exfiltration, providing a realistic end-to-end attack simulation.
- Specialization in both IT and OT/ICS environments is a meaningful differentiator for industrial organizations.s
- Detailed, remediation-focused reporting designed to drive measurable improvement over time
Cons
- Smaller firm with limited geographic footprint compared to larger consultancies; capacity for simultaneous large-scale engagements may be constrained.
- Less suitable for organizations seeking standalone phishing simulation campaigns at a workforce scale
- Pricing information is not publicly available and requires direct scoping conversations.
Ideal for: Organizations with IT and OT/ICS environments; security teams that want red team findings to benchmark and improve their security posture across multiple engagement cycles.
6. Bluefire Redteam
Headquarters: United States Best for: Organizations that want red team-grade social engineering with attention to modern techniques, including AI-augmented attack scenarios
Overview
Bluefire Redteam is a focused offensive security firm offering social engineering simulation services alongside broader red team and AI security testing capabilities. Notably, Bluefire Redteam has developed AI red teaming and prompt injection testing capabilities, positioning it well for organizations whose threat models include AI-enabled attack scenarios. Their service model emphasizes ongoing testing and actionable insights rather than point-in-time assessments.
Services offered: Social engineering simulations (phishing, vishing, smishing, physical), red team operations, AI red teaming, prompt injection testing
Pros
- One of the few providers actively developing AI red teaming capabilities alongside traditional social engineering services
- Emphasis on continuous services rather than one-off engagements aligns with mature security programs.
- Physical penetration testing is included across engagement types
- Focused offensive security practice without the overhead of a large managed services portfolio
Cons
- Smaller firm, which may affect capacity for large enterprise engagements with complex scoping requirements
- Limited publicly available case studies or client references compared to larger, more established firms
- AI red teaming is an emerging service area; the maturity of methodology varies across providers in this space.
Ideal for: Security-mature organizations whose threat model includes AI-augmented social engineering; teams running continuous security validation programs rather than annual point-in-time assessments.
7. Mandiant (Google Cloud)

Headquarters: United States (Reston, Virginia) Founded: 2004 (acquired by Google Cloud in 2022) Best for: Enterprise organizations needing red team assessments grounded in real-world incident response intelligence
Overview
Mandiant's position in the social engineering space is unique. Their red team capabilities are directly informed by frontline incident response work across some of the world's most significant breaches. When Mandiant simulates a social engineering attack, the tactics, techniques, and procedures it uses are derived from what it has observed real threat actors deploying.
Services offered: Red team assessments, social engineering (phishing, vishing, pretexting), OSINT, adversary emulation based on real-world TTPs, incident response, threat intelligence
Pros
- Unmatched intelligence feed: TTPs are derived from active incident response engagements across global breaches
- Highly realistic adversary emulation that mirrors nation-state and organized criminal group behavior
- Deep integration between red team findings and threat intelligence gives clients a genuine attacker's-eye view.
- Strong brand credibility with auditors, regulators, and enterprise procurement teams
Cons
- Premium pricing that is not suited for SMBs or organizations with limited security budgets
- Engagement timelines can be long, and scoping processes can be complex for a straightforward social engineering assessment.s
- Organizations seeking lightweight or templated social engineering testing will find Mandiant's model to be more than they need
Ideal for: Large enterprises and organizations in highly regulated industries; security teams with mature programs that want red team simulations grounded in current threat intelligence; organizations that need board-level reporting on security resilience against advanced persistent threats.
8. Bishop Fox

Headquarters: United States (Tempe, Arizona). Founded: 2005 Best for: Enterprises needing social engineering integrated into full-scope attack surface testing with strong research capabilities
Overview
Bishop Fox is one of the world's largest pure-play offensive security consultancies, with a broad service portfolio and a deep research practice. The Cosmos platform allows organizations to move beyond point-in-time assessments toward ongoing attack surface management. Their research team regularly publishes CVEs and offensive tooling, and those findings inform active engagement methodology.
Services offered: Social engineering (phishing, vishing, pretexting, physical), red teaming, penetration testing, attack surface management via Cosmos platform, application security
Pros
- One of the largest and most credentialed pure-play offensive security firms globally
- The Cosmos platform enables continuous attack surface visibility between point-in-time engagements.
- An in-depth OSINT and pretext development process is tailored to each client's specific context.
- Strong research publication history means engagements reflect novel attack paths, not just well-known ones.
- Ability to combine social engineering with technical exploitation for a full attack chain demonstration
Cons
- Enterprise-oriented engagement model carries overhead and pricing that may not suit smaller organizations.
- Engagement timelines can be extended due to demand; scheduling lead times can be significant.t
- The breadth of services means social engineering is one of many practice areas rather than a primary specialization.
Ideal for: Enterprise security teams that want social engineering as part of a broader, integrated offensive security program; and organizations managing complex environments that benefit from continuous attack-surface visibility.
9. NetSPI
Headquarters: United States (Minneapolis, Minnesota) Founded: 2001 Best for: Enterprises and large organizations needing social engineering delivered within a mature PTaaS platform with strong program management capabilities
Overview
NetSPI's social engineering engagements go beyond standard phishing templates, incorporating advanced techniques such as device code phishing, OAuth application phishing, and MFA token capture. All social engineering work is managed and delivered through the Resolve platform, which gives security teams real-time visibility into findings, remediation tracking, and SLA management.
Services offered: Email phishing (broad and spear phishing), vishing, smishing, physical social engineering, and on-site intrusion testing, red team operations, PTaaS, application and cloud penetration testing, AI/ML penetration testing, attack surface management
Pros
- Broad and well-documented social engineering capability covering email, phone, SMS, and physical vectors
- Advanced phishing techniques, including device code phishing and MFA token capture, go beyond templated campaigns
- The Resolve platform provides real-time findings visibility, remediation orchestration, and program-level reporting
- 350+ in-house testers means consistent staffing quality and capacity for large or multi-site engagements
- Physical social engineering practice is well-developed, with published real-world case studies demonstrating high-impact findings
Cons
- Enterprise-oriented model and pricing may carry more overhead than smaller organizations need for straightforward assessments.
- A platform-driven delivery model may feel less flexible for organizations that prefer a more bespoke, consultative engagement approach.
- Pricing is not publicly listed; scoping conversations are required before any cost clarity.
Ideal for: Large enterprises and highly regulated organizations that need social engineering managed within a broader PTaaS program; security teams that want real-time platform visibility into findings and remediation progress rather than static post-engagement reports.
10. Netragard
Headquarters: United States (Marlborough, Massachusetts) Founded: 2006 Best for: Organizations that want elite, research-driven penetration testing with social engineering embedded in a sophisticated, multi-phase methodology
Overview
Netragard has been operating in the offensive security space since 2006 and has built a reputation for technical depth that goes well beyond standard penetration testing. Their proprietary Real Time Dynamic Testing methodology is derived from zero-day vulnerability research and exploit development practices. Social engineering is embedded in their Platinum-tier service offering and includes custom spear-phishing and vishing pretexts, quid pro quo scenarios, and physical access testing.
Services offered: Social engineering (phishing, vishing, spear phishing, physical), web and mobile application penetration testing, network and cloud penetration testing, OSINT, security advisory and consulting, adversary emulation.
Pros
- Real Time Dynamic Testing is a proprietary methodology derived from zero-day research, not an industry-standard framework
- Social engineering at the Platinum tier is genuinely adversarial, including personalized spear phishing, vishing, and physical intrusion.
- Strong credibility and independent media recognition beyond vendor-produced content
- Tiered service structure allows organizations to match engagement depth to budget and risk profile.
- Free retest included across all service tiers
Cons
- Social engineering is only available at the Platinum tier; organizations looking for a standalone, lightweight engagement will need to commit to a broader scope.
- Boutique firm size means that the capacity for large simultaneous enterprise engagements may be limited.
- Less suitable for organizations seeking an ongoing PTaaS subscription model with continuous release-aligned testing
Ideal for: Organizations that want research-grade offensive security with social engineering as part of a comprehensive assessment; companies in banking, finance, healthcare, and software that need rigorous testing backed by deep exploit research experience.
Why Software Secured Is the Number One Choice for Social Engineering
Social engineering is not a training problem with a training solution. It is a systems problem that requires layered controls, honest measurement, and periodic adversarial validation to keep pace with an increasingly sophisticated threat landscape. The vendors on this list represent the strongest options across both categories — use them strategically, not interchangeably. For organizations that want testing built around their actual risk profile, connected to technical attack paths, and delivered with reporting that engineers and executives can act on, the starting point is clear: Software Secured.
FAQ
What is social engineering testing?
Social engineering testing is a security assessment that simulates human-targeted attacks (phishing emails, vishing calls, pretexting, and physical intrusion attempts) to evaluate whether your employees and processes can detect and resist manipulation.
What's the difference between a phishing simulation and a full social engineering test?
A phishing simulation sends fake phishing emails to employees to measure click rates and credential submission; it's a training tool focused on awareness. A full social engineering test goes further, combining phishing with vishing, pretexting, physical access attempts, and multi-stage scenarios designed to gain actual access to systems or sensitive data.
What does a social engineering engagement include?
A comprehensive social engineering engagement typically covers spear phishing campaigns targeting specific roles, vishing calls impersonating vendors or IT support, pretexting scenarios to elicit sensitive information, and in some cases physical security testing such as tailgating or badge cloning. The output is a report showing which attack vectors succeeded, which employees or teams were most vulnerable, and what procedural or training gaps to address.
How is social engineering testing different from red teaming?
Social engineering testing focuses specifically on human and process vulnerabilities while Red Teaming is a broader, objective-driven exercise that combines social engineering with technical attacks, lateral movement, and persistence to simulate a full adversary campaign. Social engineering is often a component within a red team engagement, but can also be scoped and delivered as a standalone assessment.
Who should get social engineering testing?
Any organization where employees handle sensitive data, have privileged system access, or are targeted by attackers as an entry point. It's especially valuable for companies in regulated industries like healthcare and finance, organizations that have completed technical security testing and want to assess their human layer, and teams preparing for compliance audits that evaluate security awareness controls.



.avif)
.png)
