What’s Different About an Engineering-First Pentest?
While standard pentests are often designed for auditors to meet regulatory requirements, engineering-grade tests are designed to integrate directly into developer workflows to address specific operational friction points.
Contextual Scoring
Pentesting that aligns with OWASP Top 10, SANS Top 25, ASVS Level 1, WSTG and NIST.
- Severity reflects real exploitability and deployment context
- Prioritization aligns security risk with actual engineering and business impact
Reporting as a Functional Interface
A place to give engineering, security, and IT leaders control in one place.
- Findings structured to plug directly into Jira, sprint planning, and remediation workflows
- Clear ownership, reproduction steps, and fix guidance
Collaborative Remediation
Remediation guidance, risk ratings with every vulnerability, as well as read-out report meetings.
- Direct access to pentesters for clarification, validation, and fix review
- Issues are truly resolved, not just marked “done”
See the difference for yourself
Integrations That Speed Up Remediation
Push findings straight into the tools your teams already live in, Jira, Azure DevOps, and Linear, so remediation starts immediately, ownership is clear, and nothing gets lost between a PDF and a backlog.
.png)
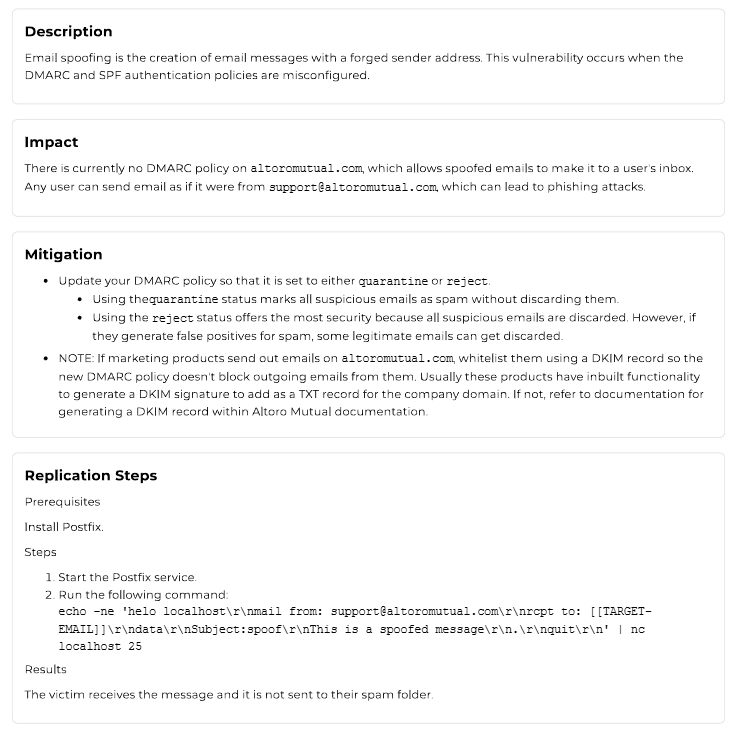
Actionable Reports
Every finding ships with calculated risk (CVSS/DREAD), crisp impact, and detailed steps to reproduce, plus concrete fix guidance, so engineers can act fast without guesswork, back-and-forth, or wasted cycles.
One-Click Retesting
Turns findings into fixes, reduces wasted engineering time, and improve both immediate remediation and long-term security maturity.
.png)
Get A Sample Report
Most pentest reports are written for auditors.
This one is designed for the people who have to fix the findings.

Case Studies
Used by engineering teams building compliant SaaS products without slowing delivery.
